- Paolo Stagno
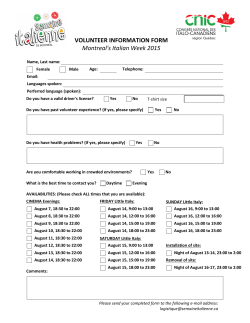
Resume Personal Information Paolo Stagno Corso Torino 13, 10095 Grugliasco, Torino (Italy) +393347145454 +390117802701 [email protected] http://voidsec.com http://paolostagno.com https://github.com/VoidSec Sex Male | Date of birth 26.07.1993 | Nationality Italian “Some things in life are unpredictable, your Security doesn’t have to be one of them” JOB APPLIED FOR Cyber Security Analyst - Penetration Tester WORK EXPERIENCE Paolo Stagno, aka VoidSec, is a Cyber Security Analyst. He’s consultant specialized in Penetration Test, Vulnerability Assessment, Cybercrime, Underground Intelligence, Network and Application Security for a wide range of clients across top tier international bank, major companies and industries. He is attending as speaker for various international conferences, like: DEFCON, BlackHat and Droidcon. He is also the leader and founder of VoidSec.com Currently attending WAPT and WAPTX certification November 2014 - Ongoing Cyber Security Analyst iDIALOGHI http://idialoghi.com Milan Area, Italy Working with very high profile clients using bleeding edge technologies in the Cyber space arena. Expert on deep hacking and Cyber warfare; focus on highly critical, strategic ICT Security and Cyber Defense issues, providing stateof-the-art, innovative Solutions and reliable Services to our global Customers. Publications APT, Social Network and Cybercrime: defensive strategies Social Network, advanced threats and Cybercrime are arguments now inextricably linked. A Security Expert is facing attacks with increasingly complex, that combine as attack vectors the technological exploitation and the weakest element: the user. In this sense, social networks have become the "hunting ground" most exploited by attackers. Report: Clusit 2015 (Italian Association for Information Security) This report presents an overview of the most significant events of cyber-crime in the last twelve months, with particular attention to the Italian Situation. Author of the paragraph: Ten Representative Incident of 2014 and data collector for statistical evidence of global attacks 2012-Ongoing Security Researcher and Penetration Tester (Freelance) VoidSec, Turin http://voidsec.com/ Penetration Testing, Vulnerability Assessment, Red Team. IT Security Research, Security Advisor, Underground Intelligence, Penetration Test, Bug Hunting, Exploit, Social Engineering, OSINT About VoidSec.com I believe that, especially in Italy, in the last few years, the underground hacking community died, not for a lack of ideas or skills but because, in our opinion, we lost two fundamental requirements: a meeting place and the possibility to share. Paolo Stagno VoidSec.com intends to give to all hackers a meeting place, where ideas can be shared freely; where: who know can return the knowledge to the community and a place where the inexperienced can learn. Publications Advisory: Minds.com Minds.com a new privacy-focused social network supported by Anonymous. HTML5 Injection Infosec Institute: Hacking communities in the Deep Web Host Header Injection & Cache Poisoning Infosec Institute: PoS Malware is More Effective and Dangerous Overview of Cybercrime in 2014 Advisory: Ghost Blogging Platform Ghost Blogging Platform, Web Application Penetration Test e Code Review Author Conferences GHOST bug, Technical Analysis Botnet: classification and analysis Advisory: Yahoo Messenger Insecure Local Data Storage POODLE bug, Technical Analysis Shellshock/Bashbug, Technical Analysis Trend Watch: Drop Hack Technical analysis of the Heartbleed vulnerability NewPosThings Hacked & Exposed Technical analysis of a PoS malware Dropper Analysis Skype Social Engineering Report: McDonald's Wi-Fi Login System - Security Advisory Interview: Anonymous against sites of Csi – La repubblica Two ethical hackers takes little to make assumptions on Anonymous "Operation Payback" Interview: software vulnerability and the underground scene in the city of Turin – La Repubblica Turin, a colony of ethical hackers Paolo Stagno (VoidSec) and Luca Poletti (Kalup), two young researchers who have found a "vulnerability" in Skype, a VOIP software: they have discovered how easy it is to deceive the assistance and steal the account of a user. More recently they have discovered a security holey in McDonald's restaurants. Inside a Bulletproof Hosting Dropper Analysis Analysis ITcms v.2 / v.3 - Multiple Vulnerabilities SQL Injection, DoS (Database Exhaustion), XSS, RFI, Cross-site request forgery Mastering Metasploit Framework Online Course This course aims to give the reader a thorough knowledge, both theoretical and operative, regarding the Metasploit Framework. No prior knowledge of the Framework is required: the students are brought from the ‘absolute beginner’ status to a level in which they can professionally use the framework. This course is also enriched with live examples and exercises to help the student better fixing concepts and ideas. Throughout the course, the Authors will share their experiences as professionals and give also education on how to present the results of a Penetration Test Speakers: Droidcon - (Turin, April 9-10, 2015) – Android (Un)Security Guidelines Best practice and guidelines for a responsible development of Android applications. What to do during the development cycle of an Android application. Speakers: Linux Day - (Turin, October.26, 2013) - Penetration testing with Linux Kali Seminars HackInBo – (Bologna, 23-24 May) – Reporter HackInBo – (Bologna, 11 October) – Reporter Page 2 / 5 Paolo Stagno Cyberia - (Torino, 14 September) – Reporter Free Libre Open Source Software with Richard Stallman Hackinbo - (Bologna, May 3, 2014) - Reporter Deftcon - (Milan, April 11, 2014) - Reporter Droidcon - (Turin, 6-7 February 2014) - Reporter Hackinbo - (Bologna, September 20, 2013) - Reporter Honors and Awards Symantec Cyber Readiness Challenge - (Rome, May 23, 2013) - 10 ° classified Challenge mode, CTF (Capture The Flag) - Diary of experience Business or sector Computer Security 07 / 2014-09 / 2014 Penetration Tester Expaway http://expaway.com Analysis of critical system Source code auditing (JAVA / C) Testing and exploitation Writing Reports Business or sector E-Recruitment 2013-2015 Web Design and Webmaster Sawa Catering Corso Svizzera 185, 10149 Torino (Italy) http://sawaristorazione.it/ Business or sector Catering 2011-Ongoing International Association Caring in Progress, Torino (Italy) http://humancaringprogress.org/ Business or sector Human health and social 2011-Ongoing Oratorio Borgis Viale Giustetti 12, 10095 Grugliasco (TO) (Italy) http://www.oratorioborgis.it Business or sector Training Services and Communications 2012-2013 Enrica Guglielmi, Grugliasco (TO) Business or sector Professional Photographer 2011-2011 Studio SG Via Pavia, 11B, 10098 Rivoli (TO) (Italy) Business or sector Human health and social 2011-2011 ASD Santa Maria, Grugliasco (TO) (Italy) Business or sector Sports Club Realization maintenance and administration of the website (Wordpress/Joomla/Drupal etc.) SEO Optimization Social Media: Creating and Managing Facebook page Monthly publications of technical documentation Database Management Evidence of statistical data Page 3 / 5 Paolo Stagno Production of flyers, graphic logos and business cards Front-end office and public relations EDUCATION AND TRAINING 2013-2014 Security Systems and Computer Networks EQF Level 6 University of Milan, Crema (Italy) http://sicurezzaonline.di.unimi.it/ Objectives such as the protection of business systems and the fight against cybercrime require research on the global market of professionals able to operate with a dual focus on programming and secure networking: 2008-2012 Analysis, Design and management of enterprise information systems and e-business secure systems. Security, privacy and intrusion prevention. Development application services over computer networks (web services). Heterogeneous distributed systems, and mission critical. Industrial Chief Specialization Computer Science EQF Level 4 Institute Amedeo Avogadro Corso San Maurizio, 8, 10124 Torino (Italy) http://www.itisavogadro.it/ Specific expertise in the field of information systems, information processing, applications and Web technologies, networks and communications equipment; Analysis, design, installation and management of computer systems, databases, networks, multimedia systems and equipment for transmission and reception of signals, programming (Java, PHP, C, Assembly 8086); Managing the lifecycle of applications that can turn to software management – service-oriented – for dedicated systems “embedded”; Project management, operating within the framework of national and international regulations concerning safety in all its forms and information protection. PERSONAL SKILLS Mother tongue Italian Other languages English UNDERSTANDING SPEECH Listening Reading B2 C1 WRITING Interaction Speaking B2 B2 B1 Preliminary English Test Levels: A1 / A2: Basic Level - B1 / B2: Intermediate - C1 / C2: Advanced Level Common European Framework of Reference for Languages Communication Skills Ability to work in teams, communicate effectively and collaborate to achieve a common goal matured during the early years of university projects, then thanks to negotiations with customers and relations with the public frontend Organizational and management skills Good ability to manage, organize workload and interact with others (colleagues and external users) thanks to the training and activities during free time. Leadership and management of human resources acquired during my volunteer experience as a trainer and facilitator. Page 4 / 5 Paolo Stagno Core Skill Professional skills Penetration Testing, Social Engineering and Red Team. Good knowledge of commercial software for computer security (Acunetix, Nessus, Core Impact, Netsparker), open source (Metasploit, Nmap, Nikto, Burp Suite, Fiddler, Open VAS) and distributions of linux specific (BackBox, Backtrack / Kali). Reverse Engineering (IDA and OllyDbg) Criticality Analysis of the Windows operating system (XP, Vista, Seven, 8) Analysis of critical systems and their vulnerability, compiling detailed reports showing the found vulnerabilities and recommending how to fix them. Practical knowledge of OWASP Developing Secure Web Applications, penetration testing Embedded Linux environments, Risk Analysis and Risk Mitigation. Source codes auditing, testing and exploitation (FindBugs, WAP, RIPS, Visual Code Grepper). Implementation and adaptation to the security standards required by the Customers of IT architectures on multiple environments. Management of corporate IT security. Penetration testing, ethical hacker, Hardening systems and implementing new structures. Study and analysis of solutions for secure systems. Monitoring of compliance on architectures according to the standard prefixes and control of conformity with the security policy document in computer science (DPS) Auditing. Develop, maintain the Information Security Policy and Security Management System. Computer Skills Programming Java, PHP, SQL, HTML, JavaScript, C, assembly 8086, Visual Basic. Sketchy knowledge of PERL, ASP, Python and .NET. Database management (MySQL phpmyadmin-). Good knowledge of Microsoft Office tools (Word ™, Excel ™ and PowerPoint ™). Managing Windows & Linux environments. Basic knowledge of graphic design applications (GIMP). Advanced knowledge of Wordpress and Joomla Other skills Good interpretation of body language and non-verbal language acquired through participation in a psychological and graphological training course Dr. Evi Crotti Voluntary activities as a trainer, educator and facilitator of a group of boys in the two years of high school. Motor skills acquired over the years thanks to the activity of parkour (acrobatic gymnastics). Driver's license Italian B (for vehicle up to 3.5 tons) Page 5 / 5
© Copyright 2026