Social Insurance, Information Revelation, and Lack of Commitmentâ
Social Insurance, Information Revelation, and Lack
of Commitment
Mikhail Golosov
Princeton
Luigi Iovino
Bocconi
March 2015
Abstract
We study the optimal provision of insurance against unobservable idiosyncratic shocks in
a setting in which a benevolent government cannot commit. A continuum of agents and the
government play an in…nitely repeated game. Actions of the government are constrained only
by the threat of reverting to the worst perfect Bayesian equilibrium (PBE). We construct
a recursive problem that characterizes the resource allocation and information revelation on
the Pareto frontier of the set of PBE. We prove a version of the Revelation Principle and
…nd an upper bound on the maximum number of messages that are needed to achieve the
optimal allocation. Agents play mixed strategies over that message set to limit the amount
of information transmitted to the government. The central feature of the optimal contract
is that agents who enter the period with low implicitly-promised lifetime utilities reveal no
information to the government and receive no insurance against current period shock, while
agents with high promised utilities reveal precise information about their current shock and
receive insurance as in economies with full commitment by the government.
We thank Mark Aguiar, Fernando Alvarez, V.V. Chari, Hugo Hopenhayn, Ramon Marimon, Stephen Morris,
Chris Sleet, Pierre Yared, Sevin Yeltekin, Ariel Zetlin-Jones for invaluable suggestions and all the participants
at the seminars in Bocconi, Carnegie Mellon, EIEF, Georgetown, Minnesota, Norwegian Business School, Paris
School of Economics, Princeton, University of Lausanne, University of Vienna, Washington University, the SED
2013, the SITE 2013, the ESSET 2013 meeting in Gerzensee, 12th Hydra Workshop on Dynamic Macroeconomics
and 2014 Econometric Society meeting in Minneapolis. Golosov thanks the NSF for support and the EIEF for
hospitality. We thank Sergii Kiiashko and Pedro Olea for excellent research assistance.
1
1
Introduction
The major insight of the normative public …nance literature is that there are substantial bene…ts
from using past and present information about individuals to provide them with insurance
against shocks and incentives to work. A common assumption of the normative literature is
that the government is a benevolent social planner with perfect ability to commit. The more
information such a planner has, the more e¢ ciently she can allocate resources.1
The political economy literature has long emphasized that such commitment may be dif…cult to achieve in practice.2 Self-interested politicians and voters –whom we would broadly
refer to as “the government” –are tempted to re-optimize over time and choose new policies.
When the government cannot commit, the bene…ts of providing more information to the government are less clear. Better informed governments may allocate resources more e¢ ciently
as in the conventional normative analysis but may also be more tempted to depart from the
ex-ante desirable policies. The analysis of such environments is di¢ cult because the main
analytical tool to study private information economies –the Revelation Principle –fails when
the decision maker cannot commit.
In this paper we study optimal information revelation and resource allocation in a simple
model of social insurance – the unobservable taste shock environment of Atkeson and Lucas
(1992). This environment, together with closely related models of Green (1987), Thomas and
Worrall (1990), Phelan and Townsend (1991), provides theoretical foundation for a lot of recent work in macro and public …nance. This set up and its extensions was used to study
design of unemployment and disability insurance (Hopenhayn and Nicolini (1997), Golosov
and Tsyvinski (2006)), life cycle taxation (Farhi and Werning (2013), Golosov et al. (2011)),
human capital policies (Stantcheva (2014)), …rm dynamics (Clementi and Hopenhayn (2006)),
military con‡ict (Yared (2010)), international borrowing and lending (Dovis (2009)). In the
key departure from that literature we assume that resources are allocated by the government,
which, although benevolent, lacks commitment. We study how information revelation a¤ects
incentives of the government to provide insurance in such settings and characterize the prop1
The seminal work of Mirrlees (1971) started a large literature in public …nance on taxation, redistribution and
social insurance in presence of private information about individuals’types. Well known work of Akerlof (1978)
on “tagging” is another early example of how a benevolent government can use information about individuals
to impove e¢ ciency. For the surveys of the recent literature on social insurance and private informaiton see
Golosov et al. (2006) and Kocherlakota (2010).
2
There is a vast literature in political economy that studies frictions that policymakers face. For our purposes,
work of Acemoglu (2003) and Besley and Coate (1998) is particularly relevant who argue that ine¢ ciencies in
a large class of politico-economic models can be traced back to the lack of commitment. Kydland and Prescott
(1977) is the seminal contribution that was the …rst to analyze policy choices when the policymaker cannot
commit.
1
erties of the optimal contract.
Formally, we study a repeated game between the government and a continuum of atomless
citizens in the spirit of Chari and Kehoe (1990) and focus on the perfect Bayesian equilibria
(PBE) that are not Pareto-dominated by other PBE. The economy is endowed with a constant
amount of perishable good in each period and the government allocates that endowment among
agents. Agents receive privately observable taste shocks that follow a Markov process, which
is assumed to be iid in the baseline version of our model. Agents transmit information about
their shocks to the government by sending messages. The government uses these messages
to form posterior beliefs about realization of agents’types and allocate resources. The main
friction is that ex-post, upon learning information about the agent’s type, the government
has the temptation to allocate resources di¤erently from what is required ex-ante to provide
incentives to reveal information. The more precise information the government has about the
agents’types, the higher its payo¤ from deviation is.
Our paper makes three contributions. First, we construct a recursive formulation of our
problem. The key di¢ culty that we need to overcome is that the value of the worst equilibrium
depends on the implicit promises made to all agents. The standard recursive techniques,
that characterize optimal insurance for each history of past shocks in isolation from other
histories, do not apply directly since information that any agent reveals a¤ects the government’s
incentives to renege on the promises made to other agents. We make progress by showing how
to construct an upper bound for the value of deviation which coincides with that value if
all agents play the best PBE and takes weakly higher value for any other strategy. This
upper bound can be represented as a history-by-history integral of functions that depends only
on the current reporting strategy of a given agent, and thus can be represented recursively.
Since the original best PBE strategies still satisfy all the constraints of this modi…ed, tighter
problem, the solution to this recursive problem allows us to uncover the best PBE. The resulting
recursive problem is very simple. It is essentially a standard problem familiar from the recursive
contract literature with two modi…cations: agents are allowed to choose mixed rather than
pure strategies over their reports and there is an extra term in planner’s objective function
that captures “temptation” costs of revealing more information.
Our second contribution is to show a version of the Revelation Principle for our settings. It
is well known that standard direct revelation mechanisms, in which agents report their types
truthfully to the government, are not e¢ cient in this type of settings. Bester and Strausz
(2001) showed that, in a repeated game between one principle and one agent whose type can
take N values, the message space can be restricted to only N messages over which agents play
2
mixed reporting strategies. These techniques do not apply to economies with more than one
agent.3 We show that in our baseline version of the model with continuum of agents and iid
shocks it is without loss of generality to restrict attention to message spaces with at most 2N 1
messages. This result follows from the fact that with iid shocks our recursive characterization
satis…es single-crossing property, and therefore all messages that give any type n the highest
utility can be partitioned in three regions: those that also give the highest utility to types
n + 1 and n
2N
1 and those that give the highest utility to only type n: There can be at most
1 of such partitions and convexity of our problem implies that it is su¢ cient to have one
message per each partition.
Our third contribution is the characterization of the properties of the optimal contract and
the e¢ cient information revelation. As in the full commitment case of Atkeson and Lucas
(1992), it is optimal to allocate resources to agents with temporality high taste shocks by
implicitly promising to increase future lifetime utility of agents with temporarily low taste
shocks. As agents experience di¤erent histories of shocks, there is a distribution of promised
utilities at any given time. We show that it is e¢ cient for agents who enter the period with
di¤erent promised utilities to reveal di¤erent amounts of information. In particular, we show
that under quite general conditions agents who enter the period with low promised utilities
reveal no information about their idiosyncratic shock in that period and receive no insurance.
In contrast, under some additional assumption on the utility function and the distribution of
shocks, agents who enter the period with high promised utilities reveal their private information
fully to the government. The optimal insurance contract for such agents closely resembles the
contract when the government can commit.
The intuition for this result can be seen from comparing costs and bene…ts of revealing
information to the government. The costs are driven by the temptation to deviate from the exante optimal plan and re-optimize. When the government deviates from the best equilibrium,
it reneges on all the past implicit promises and allocates consumption to each agent based on
its posterior beliefs about agent’s current type. Therefore, the incentives for the government
to deviate depend only on the total amount information it has but not on which agents reveal
it. On the contrary, the bene…ts of information revelation depend on the e¢ ciency gains from
better information on the equilibrium path, which in turn depend on the implicit promises
with which an agent enters the period. The general lesson is that the agents for whom better
3
See also Skreta (2006) who extends the analysis to an arbitrary type space and show the optimal selling
mechanism in a game between one buyer and one seller. Bester and Strausz (2000) provide an example of an
economy with two agents to illustrate that that with more than one agent message spaces with only N elements
are restrictive.
3
information leads to the highest e¢ ciency gains on the equilibrium path should send precise
signals to the government. In Atkeson and Lucas (1992) multiplicative taste shock environment
those are the agents with high promised utility.
Participation constraints of the government prevent the emergence of the extreme inequality, known as immiseration, which is a common feature of environments with commitment. The
optimal contract exhibits mean reversion, so that agents with low current promised utilities
receive in expectation higher future promises, and vice versa. This implies that in an invariant
distribution no agent is stuck in the no-insurance region forever, and in a …nite number of steps
he reaches a point when he reveals some information about his shock and some insurance is
provided. Thus, we show that in the invariant distribution there is generally an endogenous
lower bound below which agent’s promised utility never falls.
Our paper is related to a relatively small literature on mechanism design without commitment. Roberts (1984) was one of the …rst to explore the implications of lack of commitment for
social insurance. He studied a dynamic economy in which types are private information but
do not change over time. More recently, Sleet and Yeltekin (2006), Sleet and Yeltekin (2008),
Acemoglu et al. (2010), Farhi et al. (2012) all studied versions of dynamic economies with
idiosyncratic shocks closely related to our economy but made various assumptions on commitment technology and shock processes to ensure that any information becomes obsolete once
the government deviates. In contrast, the focus of our paper is on understanding incentives to
reveal information and their interaction with the incentives of the government. Our paper is
also related to the literature on the ratchet e¤ect, e.g. Freixas et al. (1985), La¤ont and Tirole
(1988). These authors pointed out that without commitment it is di¢ cult to establish which
incentive constraints bind, which signi…cantly inhibited further development of this literature.
Some papers have thus focused on the analysis of suboptimal but tractable incentive schemes.
We show that the problem substantially simpli…es when the principal interacts with a continuum of agents since any agent’s report does not a¤ect the aggregate distribution of the signals
received by the principal. In this case we can obtain a tight characterization of the optimal
information revelation for high and low values of promised utilities.
Our results about e¢ cient information revelation are also related to the insights on optimal
monitoring in Aiyagari and Alvarez (1995). In their paper the government has commitment but
can also use a costly monitoring technology to verify the agents’reports. They characterize how
monitoring probabilities depend on the agents’promised values. Although our environment and
theirs are very di¤erent in many respects, we both share the same insight that more information
should be revealed by those agents for whom e¢ ciency gains from better information are the
4
highest. Work of Bisin and Rampini (2006) pointed out that in general it might be desirable
to hide information from a benevolent government in a two period economy. Finally, our
recursive formulation builds on the literature on recursive contracts with private information
and a patient social planner. Work of Farhi and Werning (2007) provides recursive tools that
are particularly useful in our settings.
The rest of the paper is organized as follows. Section 2 describes our baseline environment
with iid shocks. Section 3 derives the recursive characterization and shows a version of the
Revelation Principle. Section 4 analyzes e¢ cient information revelation and optimal insurance.
Section 5 extends our analysis to general Markov shocks.
2
The model
The economy is populated by a continuum of agents of total measure 1 and the government. There is an in…nite number of periods, t = 0; 1; 2; ::: The economy is endowed with
e units of a perishable good in each period. Agent’s instantaneous utility from consuming
ct units of the good in period t is given by
tU
(ct ) where U : R+ ! R is an increas-
ing, strictly concave, continuously di¤erentiable function. The utility function U satis…es
Inada conditions limc!0 U 0 (c) = 1 and limc!1 U 0 (c) = 0 and it may be bounded or un-
bounded. All agents have a common discount factor
v = limc!0 U (c) = (1
. Let v = limc!1 U (c) = (1
) and
) be the upper and lower bounds on the lifetime expected utility of
the agents (v and v may be …nite or in…nite). For our purposes it is more convenient to work
with utils rather than consumption units. Let C
The taste shock
we assume that
t
t
takes values in a …nite set
U
1
be the inverse of the utility function.
with cardinality j j: For most of the analysis
are iid across agents and across time, but we relax this assumption in Section
5. Let
( ) > 0 be the probability of realization of 2 : We assume that 1 < ::: < j j and
P
normalize
( ) = 1: We use superscript t notation to denote a history of realization
2
of any variable up to period t, e.g.
realization of history
t
t
= ( 0 ; :::; t ). Let
t
t
denote the probability of
: We assume that types are private information.
Each agent is identi…ed with a real number v 2 [v; v] which we soon interpret as a lifetime
promised utility. All consumers with the same v are treated symmetrically. The distribution
of promises v is denoted by
. As it will become clear shortly, the initial distribution
gives
us a ‡exible way to trace the Pareto frontier of the set of perfect Bayesian equilibria.
The government collects reports from agents about their types and allocates consumption
subject to the aggregate feasibility in each period. The government is benevolent and its payo¤
is given by the sum of expected lifetime utilities of all agents.
5
2.1
The game between the government and agents
The physical structure of our environment corresponds exactly to the model of Atkeson and
Lucas (1992). The constrained e¢ cient allocations that they characterize can be achieved by
the government which is able to commit in period 0 to in…nite period contracts. We focus
on the environment without commitment. We model the interaction between the government
and individuals along the lines of the literature on sustainable plans (Chari and Kehoe (1990),
Chari and Kehoe (1993)). Before formally de…ning the game we brie‡y outline its structure.
The government does not observes agents’types, so it collects information by having the agents
submit messages. More speci…cally, at the beginning of any period t the government chooses
a message set Mt from some space M: We assume that all the sets in M are endowed with
a metric, but we will not refer to this metric explicitly. All agents observe their types and
submits messages mt 2 Mt . The government allocates consumption to agents as a function of
current and past reports.
To capture the main trade-o¤ in information revelation we assume that the government
cannot commit even within a period: it can pick any feasible allocation of resources after
collecting agents’reports. This allows for a simple and transparent analysis in our benchmark
case of iid shocks. As we discuss in Section 5, much of the analysis carries through to the case
when shocks are persistent.4
We now formally de…ne our game. We start with information sets. Let S t
summary of information available to the government at the end of period t
set recursively with S
1
= :
St 1
is the space of public histories
1
be the
1: We de…ne this
St 1:
Each period has three stages. In the …rst stage the government chooses a message set
Mt : S t
1
! M. In the second stage agents send reports about their types. Each agent i
observes the realization of his type in period t;
i;t ;
and of a payo¤ irrelevant random variable
zi;t uniformly distributed on Z = [0; 1]. Each agent chooses a reporting strategy
Mt as a function of the aggregate history
realizations hit
Realizations of
hti
1
1
= vi ; mit
t
i
1
; zit
1
S t 1 ; Mt
i;t
over
; his past history of reports and sunspot
; current realization zi;t ; and the history of his shocks
are privately observed and we call them private history. Realizations of
are privately observed and we call them personal history and denote the space of hti
by Hit
1
t
i:
vi ; mti
: To economize on notation, de…ne hti
1
1
; zit and let Hit be the space of all
4
A small recent literature on social insurance without commitment sidesteps the possibility that the government may misuse information when it deviates from equilibrium strategies. For example, Acemoglu et al.
(2010) allow agents to stop interacting with the government if it deviates, while Sleet and Yeltekin (2008), Farhi
et al. (2012) assume that shocks are iid but there is commitment within the period. All these environment are
constructed so that the information about individuals becomes obsolete if the government deviates.
6
hti : Formally, the reporting strategy is de…ned as
: St
i;t
1
Hit
M
t
i
!
(Mt ) where
(Mt ) is a set of all Borel probability measures on Mt . We assume that all agents i with
the same history choose the same strategy
i;t ;
so that we can drop the subscript i from the
histories, and that the law of large numbers holds so that strategies
i;t
generate a distribution
of reports ~ t over Mt : Finally, in the last stage of the period the government chooses utility
allocations ut for each personal history ht as a function of S t = S t
space Mt , the distribution or reports ~ t , the function ut ; and
history at the beginning of the next period, S t : Let
t and
and
t
G;t
be the spaces of feasible
to denote the whole in…nite sequence of
t and
fxt g1
t=0 :
G;t
G;t
St 1
1; M ;
t
~ t : The message
constitute the aggregate
be the government strategy in period
respectively. We use boldface letters x
Note that the public history contains the realized distribution of reports ~ t . The latter
implies that only the agents’ deviations that a¤ect ~ t will be detected and punished by the
government and the other agents. In particular, since agents are atomistic, a deviation by a
single agent has no consequences for ~ t and, hence, will not be detectable by the other players.
For our purposes it is useful to keep track of two objects, the distribution of the agents’private histories and that of personal histories. For any S t = S t
t
as the measure of agents with histories ht ;
Borel set At of [v; v]
where At
1
Mt
t
set A of
t
is a Borel set of H t
some Borel set of Mt
Let
Zt
At jS t =
t t
t (h jS )
H t as
Z
Z
At
t 1
: It is de…ned recursively. Let
1 jS
1
Bm
1
=
: Any
Bz
B
and Bm ; Bz ; B are the mt -, z-, and -sections of
: The measure
dat
t t t
t (h ; jS )
~ t ; ut de…ne
can be represented as a product At = At
1
t 1
1; M ;
t
t 1
t
ht ; t jS t over space H t
dz
(d )
t
dmjS t
1
; Mt ; at
t
is de…ned as
1 ; z;
:
be the measure of agents with personal histories ht ; de…ned for each Borel
t
AjS
t
=
Z
t
t
A
t
jS t :
(1)
We require the government’s strategy to be feasible, so that it satis…es for any S t =
St
1; u
t
Z
C ut
; St
d
Ht
t
Citizens’strategies induce posterior beliefs pt over
ht
and
St
jS t
e:
t
: These beliefs are de…ned for all
and satisfy Bayes’rule, i.e. that for any Borel set A of H t and any t ;
Z
t t
pt t jS t ; h t dhjS t = t A
jS whenever t AjS t > 0:
A
7
(2)
(3)
Finally, we de…ne continuation payo¤s for agents and the government. Any pair ( ;
generates a stochastic process for utility allocation u: We use E(
pectation of the random variable xt :
St
Ht
measures generated by strategies ( ;
G) ;
t
and E(
St
;
;
G)
G)
xt to denote the ex-
! R with respect to the probability
G)
Ht
[xt jA] to denote the conditional ex-
t:
pectation given some Borel subset A of
The lifetime utility of agent v is
P1 t
then E( ; G )
t ut jv : Since the government is benevolent and utilitarian, its payo¤
t=0
R
P1 t
P1 t
is E( ; G )
E( ; G )
(dv) :
t ut =
t ut jv
t=0
t=0
De…nition 1 A Perfect Bayesian Equilibrium (PBE) is a strategy pro…le (
;
G)
and a belief
system p such that conditions (2) and (3) are satis…ed, and both agents and the government
choose
and
G
as their best responses, i.e.
Agents’ best response: for every S T 1 ; MT ; hT ; T ;
" 1
#
X
t T
T 1
T T
E( ; )
; MT ; h ;
E(( 0 ;
t ut S
i
G
i
);
G
t=T
0
i
for all
2
E(
;
G
)
1
X
t T
t ut
S
T 1
T
; MT ; h ;
t=T
(4)
and i.
n
Government’s best response: for every S~T 2 S T
"
)
"
1
X
t T
t ut
S~T
t=T
#
Z
E(
;
0
G
)
"
1; ST
1
X
o
t T
;
t ut
S~T
t=T
#
for all
0
G
2
G:
(5)
We focus on equilibria that maximize the payo¤ of the utilitarian government subject to
delivering lifetime utility of at least v to an agent that belongs to family v: We call it a best
equilibrium and de…ne it as follows
De…nition 2 A triple (
;
G; p
E(
;
) is a best equilibrium if it is a PBE such that
" 1
#
X
t
v for all v;
t ut v
G)
(6)
t=0
and there is no other PBE ( 0 ;
government,
E(
0;
0
G
)
0 ; p0 )
G
"1
X
t
that satis…es (6) and delivers a higher payo¤ to the
t ut
t=0
Throughout the paper we assume that
assume that
#
> E(
;
G
)
"
1
X
t=0
t
t ut
#
:
is such that a best equilibrium exists. We further
is such that (6) holds with equality in a best equilibrium. This assumption
8
T
#
simpli…es the recursive formulation since all the “promise keeping” constraints can be de…ned
as equalities in that case. Without this assumption our period 0 recursive formulation would
have to be de…ned as an inequality, which would make notation more bulky but not a¤ect any
of our results.
3
The recursive problem and the Revelation principle
In this section we discuss two intermediate results that are necessary for our analysis of optimal
information revelation. First, we derive the recursive problem solution which characterizes the
optimal reporting strategy and consumption allocation in best PBEs. Recursive techniques
are the standard tool to solve dynamic contracting problems, which essentially allow to solve
for optimal insurance after any given history of shocks separately from the other histories.
In our game-theoretic settings the standard approach to constructing Bellman equations is
not applicable: the government’s incentive to deviate from a best equilibrium depends on the
reporting strategies of all agents making the usual history-by-history separation of incentives is
impossible. To overcome this di¢ culty, we consider a constrained problem in which we replace
the function that characterizes the value of deviation for the government with another function
which is linear in the distribution of the past histories of reports. We show that this function
can be chosen such that a solution to the original problem is also a solution to the constrained
problem. The advantage is that the linearity of the constrained problem in the distribution
of past reports allows us to solve for the optimal contract recursively, history-by-history. The
key insight for this construction is that the Lagrange multiplier on resource constraint in the
best one shot deviation from best equilibrium strategies summarizes all relevant information.
The second result of this section characterizes the minimum dimension of the message space
M that is needed to support best PBEs. Reduction of an arbitrarily message space M to a
smaller dimension object is important for tractability of the maximization problem. This step
is similar in spirit to invoking the Revelation Principle in standard mechanism design problems
with commitment, and we refer to this result as the (generalized) Revelation principle.
Although these steps are crucial for our ultimate goal – characterization of e¢ cient information revelation – these tools are of interest in themselves. A lot of environments without
commitment share the feature that value of deviation for the “principal”depends on actions of
many agents, and the recursive techniques developed in our settings should also be applicable
to such environments. To the best of our knowledge, there is no version of the Revelation
Principle for economies with multiple agents when the principal lacks commitment. A well
known paper by Bester and Strausz (2001) developed a version the Revelation Principle for an
9
economy with one agent, but their approach and the main result do not extend to multi-agent
settings.
3.1
The recursive problem
We start by describing a PBE that delivers the lowest payo¤ to the government, to which we
refer as the worst PBE. It is easy to show that there are worst equilibria in which no information
is revealed.5 To see this, let m? (M ) be an arbitrary message from a set M 2 M. Consider a
strategy pro…le (
w;
w)
G
in which all agents report message m? (M ) with probability 1 for all
M , and the government allocates the same utility uw
t =C
The beliefs
pw
Lemma 1 (
that satisfy (3) are given by
w;
w ; pw )
G
pw
t
t
jht ; S t
1 (e)
=
t
for any message m it receives.
t
for all ht ; S t :
is a worst PBE.
Proof. The best response of the government to agents’reporting strategy
w
is to allocate
the same utility to all agents since its beliefs pw do not depend on m and C is strictly convex.
Given this allocation rule, playing
w
is optimal for agents, therefore (
that delivers the government payo¤ U (e) = (1
) : Strategy
w
G
w;
w;
w ; pw )
G
is a PBE
is feasible for any reporting
strategy that agents choose, so the government can attain payo¤ U (e) = (1
which proves that (
w ; pw )
G
) in any PBE,
is a worst PBE for the government.
Standard arguments establish that best equilibria are supported to reverting to the worst
PBE following any deviation of the government from its equilibrium strategies. We split
our problem in two parts. First, we …x any sequence of message sets M and describe the
maximization problem that characterizes the best PBE given that sequence of message sets,
which we call the best equilibria given M: We then show that the same payo¤ can be achieved
with a much simpler message set that has only a …nite number of messages. That set is
independent of M and hence without loss of generality it can be chosen as the message set in
the best PBE.
We start with several preliminary observations that simplify the notation. Since there is no
aggregate uncertainty the aggregate distribution of reports and allocations is a deterministic
sequence. Therefore, it is redundant to keep track of the aggregate history S t in best equilibria
and we drop this explicit dependence from our notation. Moreover, without loss of generality
we can restrict attention to reporting strategies
5
t
that depend on ht
1;
zt and
t;
but not
In fact, a stronger statement is true that in any worst equilibrium no information is revealed. This statement
follows from our Lemma 2.
10
on the past history of shocks
since as long as
ht ;
t
t
t 1 6
:
This results holds more generally with Markov shocks,
t 1
follows a Markov process,
is payo¤ irrelevant and agents with the same
can replicate each other strategies for all past
t 1
: This implies that all information
about agents at the beginning of period t can be summarized by the distribution of reports
t 1:
We now turn to setting up the maximization problem that characterizes best equilibria
given M: Since any deviation by the government from a best equilibrium triggers a switch to
the worst PBE, it is su¢ cient to consider only the best one-shot deviation from equilibrium
strategies by the government. The government that observes the distribution of personal
~ t ( t ) de…ned as
histories t can achieve the maximum payo¤ W
~ t ( t) =
W
subject to
Z
sup
Ht
fu(h)gh2H t
Z
E
C (u (h)) d
t
[ jh] u (h) d
e:
t
Ht
t
(7)
(8)
Therefore, any best equilibrium given M is a solution to
1
X
max E
u;
t
t ut
(9)
t=0
subject to (2),
E
1
X
s t
~ t ( t) +
W
s us
s=t
E
1
X
t
t ut
E
0
t=0
and
1
X
U (e) for all t;
1
t
t ut
for all
0
(10)
(11)
t=0
E
"
1
X
t
t ut
t=0
#
v = v:
(12)
The main di¢ culty in the analysis of problem (9) is that the sustainability constraint (10)
~ t ; which is a non-linear function of the past reports embedded in the probability
depends on W
~ t with a function that (i) is linear in t 1 ;
distribution t 1 : To make progress, we replaced W
~ t for all
(ii) is weakly greater than W
t;
~ t at a best equilibrium’s distribution of
and (iii) equals W
reports. This de…nes a more constrained maximization problem for which the best equilibrium
In the Supplementary Material we show that for any PBE ( 0 ;
delivers the same payo¤ to all agents and the government as ( 0 ;
( 0 ; 0G ; p0 )) and has the property that t does not depend on t
6
11
0
0
G; p )
0
0
G; p )
1
:
there is another PBE ( ; G ; p) which
(i.e. ( ; G ; p) is payo¤ -equivalent to
is still a solution. The linearity of the constraining function in
t 1
allows us to write the
constrained problem recursively.
Let (u ;
by
: Let
) be a solution to (9) and
w
t
be the distribution of personal histories induced
0 be a Lagrange multiplier in problem (7) given
t:
For any mapping
:
(Mt ) de…ne
Wt ( ) =
max
fu(m)gm2M
t
Z
w
t C
( u (m)
Mt
w
t e:
(u (m))) (dmj ) (d ) +
E [ jm].
Function Wt plays an important role in our analysis: We show that
R
(13)
w 0
w
t C (u
We use fuw (m)gm2Mt to denote the solution to (13), which is given by equation
!
Wt ( t ) dzt d
(m)) =
t 1
is an
upper bound for Wt ( t ) that satis…es the three properties needed for recursive characterization.
Before formally proving this result, it is useful to introduce some de…nitions. We say that
P
( ) = 1 a.s., i.e. for almost every
reporting strategies are uninformative if E [ jm] =
message m with respect to the measure generated by
. Uninformative reporting strategies
reveal no additional information other than the unconditional expectation of : All other
strategies are called informative. We also need to generalize the notion of the envelope theorem
for Wt : For any
and
0
de…ne a derivative of Wt ( ) in the direction
@Wt ( )
@ 0
Wt ((1
lim
0)
) +
Wt ( )
#0
0
as
:
With these de…nitions we can state the following lemma, which is important for all subsequent
analysis.
w
t
Lemma 2 The multiplier
and, therefore,
uw
is uniformly bounded away from 0 and belongs to a compact set
(m) belongs to a compact set in the interior of [(1
) v; (1
) v] for all
: The family of fWt gt and all the families of its directional derivaties are uniformly bounded.
Function Wt is well de…ned, convex, and is minimized if and only if
For any
t;
t 1
~ t ( t)
W
with equality if
t;
t 1
=
Z
Wt
t
Ht
t; t 1 :
0 is well-de…ned
The derivative @Wt ( ) =@
Z
@Wt ( )
=
( uw (m)
@ 0
Mt
w
t C
jht ;
for all
(uw (m)))
12
dzd
0
is uninformative.
(14)
t 1
and satis…es
0
(dmj )
(dmj )
(d ) :
(15)
Consider now a modi…ed maximization problem (9) in which we replace (10) with
Z
1
X
s t
Wt t jht 1 ;
dzd t 1 +
E
U (e) :
s us
1
t
H
s=t
The constraint set is tighter in the modi…ed problem, but (u ;
straints, therefore (u ;
(16)
) still satis…es all the con-
) is a solution to the modi…ed problem. One can then use standard
techniques (see, e.g. Marcet and Marimon (2009) and Sleet and Yeltekin (2008)) and use
Lagrangian multipliers to re-write it as
L = max E
u;
1
X
t [ t ut
tC
(ut )
t Wt ]
(17)
t=0
1
subject to (11) and (12) for some non-negative sequences
t ; t ; t t=0 , with a property that
^
; with strictly inequality if and only if constraint (16) binds in period t:7 We
t
t= t 1
interpret ^ as the e¤ective discount factor of the government in the best equilibrium. It is
t
greater than agents’discount factor
because the government also needs to take into account
how its actions a¤ects the sustainability constraints in the future. This is a general result
about the role of the lack of commitment on discounting that was highlighted, for example, by
Sleet and Yeltekin (2008) and Farhi et al. (2012).
The maximization problem (17) shows costs and bene…ts of information revelation. The
more information the agents reveal, the easier it is for the planner to maximize the costweighted utility function of the agents,
t ut
tC
(ut ) : At the same time, better information
also increases the temptation to deviate, captured by the term
t Wt :
This trade-o¤ is at the
heart of our characterization in Section 4.
We make two assumptions on the properties of these Lagrange multipliers which we maintain throughout the analysis, lim sup
t
> 0 and lim inf
t
> 0: These conditions simplify
technical arguments and in the Supplementary material we provide su¢ cient conditions for
C that ensure that these assumptions are satis…ed. Since the Langrange multipliers should
satisfy these properties much more generally – for example whenever the economy converges
to an invariant distribution and the long-run immiseration is a feature of the optimal contract
with full commitment –we opted to make assumptions on the multipliers directly.8
An important simplifying feature of the modi…ed maximization problem and the Lagrangian
(17) is that the distribution of past reports
t 1
enters the objective function and the con-
7
This representation is possible since allowing the government and agents to condition their strategies on
z convexi…es the maximization problem (9). The formal arguments are straightforward but cumbersome, we
present their sketch in the Supplementary Material.
8
Immiseration is a common feature of long-term contracts with commitment. See Ljunqvist and Sargent
(2004) for a textbook discussion and Phelan (2006) and Hosseini et al. (2013) for recent contributions to the
literature. We discuss existence of the invariant distribution in Section 5.1.
13
straints linearly. This allows us to solve for the optimal allocations and reporting strategies
separately for each history ht
1:
We do so by extending the recursive techniques developed by
Farhi and Werning (2007) who study an economy with commitment but in which the principal
is more patient than agents.
Let k0 (v) be the value of the objective function (17) for family v; de…ned as
" 1
#
X
1
k0 (v) =
max E
t ( t ut
t C (ut )
t Wt ) v
0 u;
subject to (11) and (12). The Lagrangian de…ned in (17) satis…es L =
Similarly we can de…ne9
kt (v) =
1
max E
t u;
(18)
t=0
"
1
X
s us
t+s
t+s C
(us )
t+s Ws
s=0
R
v
0 k0 (v)
#
(dv) :
(19)
subject to (11) and (12). The next proposition shows the relationship between kt (v) and
kt+1 (v) :
Proposition 1 The value function kt (v) is continuous, concave, di¤ erentiable with limv!v kt0 (v) =
1: If utility is unbounded below, then limv!
0
1 kt (v)
= 1; if utility is bounded below, then
limv!v kt0 (v) = 1. The value function kt (v) satis…es the Bellman equation
h
^
kt (v) =
max
E
u
t C (u) + t+1 kt+1 (w)
fu(m;z);w(m;z); ( jz; )g(m;z)2M
t
( jz; )2 (Mt )
Z
t Wt
i
(20)
subject to
h
i
E ^u + wj^; z
v = E [ u + w]
h
i
E 0 ^u + wj^; z for all z; ^;
(21)
0
(22)
Without loss of generality, the optimum is achieved by randomization between at most two
points, i.e. one can choose z 2 [0; 1] and set (u ( ; z 0 ) ; w ( ; z 0 ) ; ( jz 0 ; )) = (u ( ; z 00 ) ; w ( ; z 00 ) ; ( jz 00 ; ))
for all z 0 ; z 00
z and all z 0 ; z 00 > z:
Most of the proof of this proposition follows the arguments of Farhi and Werning (2007)
and is provided in the Supplementary materials. The solution to this Bellman equation is
attained by some functions uv;t (m; z) ; wv;t (m; z) ; and
v;t (mjz;
). In what follows we will
drop explicit dependence on t whenever this will not cause confusion. We can use these policy
functions to generate recursively ut and
t:
Standard arguments establish when these (u; )
are a solution to the original problem (9).
Variables (u; ) = fut ; t g1
t=0 are de…ned over slightly di¤erent spaces in problems (18) and (19). The
1
sequence of message sets is fMt g1
t=0 in (18), while it is fMs+t gt=0 in (19):
9
14
Proposition 2 If (u; ) obtains a maximum to (18), then it is generated by (uv ; wv ;
(u; ) generated by (uv ; wv ;
v)
v) :
If
is such that
t
lim E
t!1
vt = 0
(23)
then it is a solution to (18).
Condition (23) can be veri…ed in the same way as in Farhi and Werning (2007).
3.2
The Revelation Principle
The recursive problem (20) is similar to the usual recursive dynamic contract formulation
with commitment with two modi…cations. First, agents play a mixed reporting strategy over
set M rather than a pure reporting strategy over set
t Wt
: Second, there is an additional term
that captures the cost of information revelation. In this section we further simplify
the problem by showing that incentive constraints (22) impose a lot of structure on agents’
reporting strategies and simplify the message space that needs to be considered in best PBEs.
Since incentive constraints (22) hold for each z; we drop in this section the explicit dependence of strategies on the payo¤ irrelevant variable, and our arguments should be understood to
apply for any z: Let fu (m) ; w (m)gm2Mt be any allocation that satis…es (22). Let Mt ( )
be the subset of messages that give type
the highest utility, i.e.
u m0 + w m0
u (m) + w (m)
for all m 2 Mt ( ) ; m0 2 Mt :
Sum this inequality with an analogous condition for type
0
0
u (m)
u m0
Mt
0
to get
for all ; 0 ; m 2 Mt ( ) ; m0 2 Mt
0
:
(24)
One immediate implication of this equation is that any incentive compatible allocation is
monotone in types, i.e.
>
0
implies u (m)
u (m0 ) and w (m)
w (m0 ) : It follows that
each message set Mt ( i ) can be partitioned into three regions: the messages that also belong
to Mt (
i+1 ) ;
the messages that also belong to Mt (
i 1 ),
and the messages that do not belong
to any other Mt ( j ) :
The next proposition shows that it is without loss of generality to assume that agents send
only one message per each partition. Since there can be at most 2j j
1 of such partitions, it
also gives an upper bound on the cardinality of the message space needed in best PBEs.
Proposition 3 Any best PBE is payo¤ equivalent to a PBE in which agents report no more
than 2j j
1 messages after any history ht : Furthermore such PBE can be constructed so that
if m0 6= m00 then the utility allocation in equilibrium, ut , satis…es ut ht ; m 6= ut ht ; m
^ :
15
We brie‡y sketch the key steps of the arguments. Consider any partition Mt ( i )\Mt (
i+1 ) :
Equation (24) implies that (u (m) ; w (m)) must be the same for all m 2 Mt ( i ) \ Mt (
i+1 ) :
Therefore, all reporting strategies
that keep the same probability of reporting messages m 2
=
h
i
^ kt+1 (w) .
Mt ( i )\Mt ( i+1 ) have the same on-the-equilibrium-path payo¤ E
u
C
(u)
+
t+1
t
Thus, in a best BPE the reporting of messages in Mt ( i ) \ Mt (
i+1 )
must minimize the o¤-
the-equilibrium-path payo¤ E [ t Wt ]. Convexity of Wt implies that such reporting strategy
keeps posterior beliefs of the government the same for all m 2 Mt ( i ) \ Mt (
without loss of generality to allow only one message for each Mt ( i ) \ Mt (
i+1 ) :
Then it is
i+1 ) :
The reverse arguments allow to reach the same conclusion for the subset of Mt ( i ) that does
not intersect with any other Mt ( j ) ; which we denote Mtexcl ( i ) : Conditional on observing
any message sent with a positive probability from subset Mtexcl ( i ) ; the government learns
that the sender is type
i
with certainty. Therefore the o¤-the-equilibrium-path payo¤ does
not depend on the exact probability with each type
i
reports messages in Mtexcl ( i ) : Strict
convexity of the on-the-equilibrium-path payo¤ implies that the government chooses that same
(u (m) ; w (m)) for all m 2 Mtexcl ( i ), which again implies that it is without loss of generality
to restrict attention to only one message.
Proposition 3 is very useful for the characterization of the optimal incentive provision and
information revelation in the next section. It also allows us to prove a version of the Revelation
Principle in our economy. Let M be any set of cardinality 2j j
1:
Corollary 1 Any best PBE given M is payo¤ equivalent to a best PBE given Mt = M
for all t: The incentive constraint (22) for such equilibrium can be written, for each z; as
(m2i
1 j 2i 1 )
> 0 and
i u (m2i 1 )
(mj i ) [( i u (m2i
1)
+ w (m2i
+ w (m2i
1 ))
1)
i u (m)
+ w (m) ;
(25)
( i u (m) + w (m))] = 0 for all i = 1; ::; j j; m 2 M :
This result shows that in general the cardinality of message space with a continuum of
agents is …nite but bigger than the cardinality of the message space with only one agent. In
the latter case Bester and Strausz (2001) showed that without loss of generality one can restrict
attention to a message space M =
: Their result does not extend to economies with multiple
agents.10 Corollary 1 shows that even with a continuum of agents the dimensionality of the
message space remains small.
10
See Bester and Strausz (2000) for a counterexample with two agents.
16
4
Characterization
In this section we characterize properties of the e¢ cient information revelation. We start with a
simpli…ed environment that illustrates the main trade-o¤s very transparently. We then extend
the insights developed by this example to our general settings.
4.1
A simpli…ed environment
We make two simplifying assumptions in this section. First, we assume that the government
can deviate from its implicit promises in period t only if it deviates in period 0. This simpli…es
the analysis of the best equilibrium as it is su¢ cient to ensure that government’s sustainability
constraint (10) holds only in period 0. This case is isomorphic to our Lagrangian formulation
with
t
= 0 for all t > 0: Secondly, we assume that agents’preferences can be represented by
a utility function U (c) = ac1=a when 1=a < 1; with U (c) = ln c when 1=a = 0:
Under the …rst simplifying assumption the Lagrangian (17) can be written, up to a constant,
as
(
L = max E
u;
1
X
t
tC
(ut )
0 W0
t=0
)
subject to (11) and (12). First, consider the sub-game starting from t = 1: Since the sustainability constraints do not bind for all t
1; the standard Revelation principle applies and the
maximization problem that characterizes the optimal allocations is identical to that in Atkeson
and Lucas (1992). It is easy to show that the value function with CRRA preferences takes the
form
1 (v)
= const jvja when 1=a 6= 0 and
For any reporting strategy
0 (v;
2
)=
1 (v)
(M0 ) in period 0, let
0 (v;
0C
(u) +
max
fu(m);w(m)gm2M
subject to (21) and (22). Function
= const exp (v) when 1=a = 0:
0 (v;
E [
) be de…ned as
1 (v)]
0
) is interpreted as the value function for the govern-
ment on the equilibrium path if an agent plays reporting strategy : It inherits the homogeneity
property of function
1;
namely
0 (v;
) = d ( ) jvja for some constant d ( ) :
If no public randomization is allowed, the actual value function
0 (v)
= max
0 (v;
)
0 W0 (
0 (v)
is given by
):
With public randomization the maximum is taken over the convex hull of the function on the
right hand side.
Consider …rst the case when j j = 2 and agents can only play two reporting strategies:
a full information revelation strategy
in ;
when each type reports a distinct message with
17
un ;
probability 1, and a no information revelation strategy
when each type randomizes between
all messages with the same probability. Since the former strategy has higher payo¤ both onand o¤- the equilibrium path, d
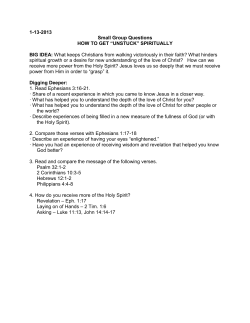
Figure 1 plots
0 (v;
)
in
0 W0 (
> d(
) for
un )
in ;
2
ization. The key observation is that function
un ) only
0 W0 (
un gives higher
in
and W0
un
; as well as
in
;
0
> W0 (
0 W0
un ) :
0 (v)
in
with public random-
intersects
0(
;
un )
once, from below at some point v2 : This shows that the uninformative strategy
in
value to the government than
for all v < v2 and lower value for all v > v2 :
Allowing public randomization may further increase the government’s payo¤ and create an
intermediate region (region (v1 ; v3 ) on the graph) in which the reporing strategy is stochastic
but it does not alter the main conclusion: no information revelation is optimal for low values
of v and full information is optimal for high values of v.
To understand the intution for this result, it is useful to compare the on the equilibium
path bene…ts of information revelation,
costs W0
in
W0 (
un ) :
0
in
;
0(
;
un ) ;
to the o¤ the equilibrium path
Given our CRRA assumption, it is easy to see that the bene…ts
are monotonically increasing in v; equal to zero as v ! v and to in…nity as v ! v: The o¤ the
equilibrium path costs of information revelation do not depend on v: Therefore, there must
exist a region of low enough v where the costs of better information revelation exceed the
bene…ts and a region of high enough v where the opposite conclusion holds.
This conclusion does not depend on the fact that we restricted attention to only two
reporting strategies. When j j = 2; any
the government satis…es d
un
and
in
un ) :
> d ( ) and W0 ( ) > W0 (
have higher payo¤ than
This implies that reporting
for low and high values of v respectively.
κ(v)
strategies
in
that reveals some but not all information to
⇐
no info
⇒
full info
v
1
v
Figure 1: Value functions in the simpli…ed example. Solid line:
in
in
un
; dashed: un
0 (v)
0
0 (v)
0W
0W ( 0 ) :
When j j > 2; it is still true that W0 ( ) > W0 (
18
v
2
un )
0
3
(v) with public randomization, dotted:
and therefore no information revelation
is optimal for low enough v. However, full information revelation no longer gives strictly higher
value than any other reporting strategy on the equilibrium path. The reason for it is that
bunching might be optimal even in standard mechanism design problems with commitment.
Our result for high values of v extends if the distribution of types is such that no bunching
is desirable with commitment (equation (33) provides a su¢ cient condition for that). More
generally, it can be shown that some information revelation is desirable for high v, in particular
it is optimal for
1
to reveal his type perfectly.
Finally, we comment on the role of the assumption of constant relative risk aversion. Our
arguments for no information revelation for low values of v only used the fact that
un
provides
the lowest value to the government o¤ the equilibrium path. This is true for any preferences.
The arguments for e¢ ciency of full information revelation rely on the fact that
0 (v;
0
v;
in
) becomes unboundedly large for high values of v: A su¢ cient condition for this is that
the absolute risk aversion goes to zero as consumption goes to in…nity, and our conclusion
holds for all preferences satisfying this condition.
This example illustrates the general principle that goes beyond the particular taste-shock
model that we consider in this paper. Since the o¤ the equilibrium path costs of information
revelation do not depend on past promises (the principal simply reneges on them when deviates)
but the bene…ts do, it is optimal to reveal less information for those agents for whom the on
the equilibrium gains are lowest. The gains from better information are monotone in v in the
taste shock economy that we consider in this paper; which allows us to get sharp cut-o¤s, but
the general principle holds regardless of this property.
4.2
Characterization of the general case
In this section we study e¢ cient information revelation in our baseline model of Section 3. Let
(uv ; wv ;
v)
be a solution to (20). To streamline the exposition, in the body of the paper we
focus on interior optimum when the lower bound U (0) does not bind; many arguments are
simpler if the lower bound binds.
We start with two key optimality conditions. The …rst order conditions for uv and wv can
be re-arranged as
^
t+1
E
v
0
kt+1
(wv ) jz = kt0 (v)
(26)
C 0 (uv ) jz :
(27)
and
kt0 (v) = 1
tE
v
The …rst condition describes the law of motion for promised utilities. Since ^ t+1
19
with strict
inequality when the sustainability constraint binds in period t + 1; it shows a version of meanreversion in promised utilities. Since kt and kt+1 are concave functions with interior maxima,
it implies that period t + 1 promises have a drift towards the value that maximizes kt+1 : This
drift component implies higher future promises for low-v agents and lower promises for high-v
agents. This mean-reverting drift helps the government to relax sustainability constraints in
future periods. The second condition provides a linkage between promised and current utility
allocations.
For our purposes it is important to establish bounds for uv and wv : The optimality conditions (see Appendix for details) imply that
1
kt0 (v)
tC
1
0
(uv (m; z))
1
kt0 (v)
j j;
(28)
and
% 1
kt0 (v) +
1
^
t+1
!
1
0
kt+1
(wv (m; z))
= ^ t+1 ; %
for some numbers %; % with a property that %
kt0 (v) +
% 1
1
= ^ t+1 ! 0 as
^
j j
t+1
!
1
(29)
! 0:
Equation (28) shows the role of private information. If agents’ types were observable,
the planner would equalize the marginal costs of providing 1 util to type , 1
1
tC
0 (u) ;
to the shadow cost of past promises, kt0 (v) ; while allocating the same promised utility w
to all types. This would give more consumption to higher
types, which is not incentive
compatible. With private information the dispersion of current period consumption allocations
is smaller, which can be seen by the bounds (28). Equation (29) shows, in addition, how the
sustainability constraints in future periods interact with the provision of incentives in the
current period. It shows that bounds for future promises 1
0
kt+1
(wv ) shrink as v ! v:
When future sustainability constraints bind, the government realizes that more dispersion of
inequality tomorrow makes it harder to sustain e¢ cient outcomes, which limits the dispersion
of promises that the government gives and prevents the long run immiseration.
Conditions similar to (26)-(29) also appear in the problems in which the government can
fully commit (see Atkeson and Lucas (1992) and Farhi and Werning (2007)). Our analysis
generalizes those conditions to the environments with no commitment. A novel feature of such
environments is that complete information revelation is generally suboptimal. We next turn
to the characterization of the e¢ cient information revelation.
Suppose that it is optimal for type
to randomize between messages m0 and m00 . The
20
optimality for the reporting strategy
uv m00 ; z
t
00
uw
v m ;z
w
t C
together with the envelope theorem yields11
uv m00 ; z
tC
uv m0 ; z
=
v
tC
uv m0 ; z
00
uw
v m ;z
+ ^ t+1 kt+1 wv m00 ; z
(30)
+ ^ t+1 kt+1 wv m0 ; z
0
uw
v m ;z
w
t C
0
uw
v m ;z
:
Equation (30) captures bene…ts and costs of information revelation. The left hand side of
the equation captures the bene…ts of better information revelation on the equilibrium path.
It compares the “cost-weighted” utility that the government obtains for type
messages m0 and m00 : This term is the general form of the expression
v;
0
if it receives
in
0 (v;
un )
that appeared in our simpli…ed example in Section 4.1. The right hand side of the equation
captures the cost of information revelation o¤ the equilibrium path. If message m00 reveals
more information about
further from
than m0 ; in a sense that the expectation of
conditional on m00 is
than the expectation conditional on m0 ; this expression is positive. The right
hand side of (30) is the analogue of
0
W0
in
W0 (
un )
in Section 4.1.
Equation (30) develops the key intuition for e¢ cient information revelation. First, consider
information revelation for low values of v: Bounds (28) and (29) imply the expression on the
left hand side of (30) converges to zero as v ! v; so that the gains from information revelation
disappear for low values of v. Therefore, the optimal reporting strategy must converge to
a strategy that minimizes the o¤ the equilibrium path cost of information revelation. Such
strategy must be uninformative by Lemma 2. Note that the uninformative strategy assigns
the same posterior belief for any reported message, so that that right hand side of (30) is zero.
In the Appendix we prove a stronger result that the uninformative strategy is optimal for all
v su¢ ciently low.
Theorem 1 Suppose that the sustainability constraint (10) binds in periods t and t + 1: There
exists vt > v such that for all v 2 v; vt
strategy
v
the allocation (uv ; wv ;
v)
does not depend on z;
is uninformative and (uv (m) ; wv (m)) = (uv (m0 ) ; wv (m0 )) for all m; m0 :
We now turn to the analysis of information revelation for high values of v: Consider the
case when j j = 2: By Proposition 3 we can restrict attention to at most 3 messages, such that
reporting two of those messages reveals the type of the sender perfectly. Therefore the left
hand side of (30) compares on-the-equilibrium-path bene…ts from a message that reveals full
information about a sender and a message that reveals only some of the information. Bounds
Formally, we take a derivative of v in the direction 0 ; de…ned as 0 (m0 j ; z) =
(m00 j ; z) = 0 and 0 (mj ; z) = v (mj ; z) for all other m; ; and apply (15).
11
0
21
v
(m0 j ; z) +
v
(m00 j ; z) ;
(28) and (29) can be used to show that as long as the coe¢ cient of absolute risk aversion,
U 00 (c)=U 0 (c) goes to zero for high c; the informational gains from better information must go
to in…nity as v ! v: Since the informational costs are bounded by Lemma 2, this implies that
equation (30) cannot hold and each agent must reveal his type fully for all v high enough.
Formally, suppose that utility satis…es
Assumption 1 (decreasing absolute risk aversion) U is twice continuously di¤ erentiable
and
lim U 00 (c) =U 0 (c) = 0:
(31)
c!1
We say that
messages as type
v
reveals full information about type
i
with positive probability.
i
if no type j 6= i sends the same
Theorem 2 Suppose that Assumption 1 is satis…ed and j j = 2: Then there exists vt+ < v
vt+ ;
such that for all v
v
reveals full information about each type.
Previous arguments can also be extended for the …rst and the last type of arbitrary message
spaces.
Corollary 2 Suppose that Assumption 1 is satis…ed.
1. (no informational distortions at the top). Then
1
v
reveals full information about
for all v su¢ ciently high.
2. (no informational distortions at the bottom). Suppose in addition that %
j j 1
j j
information about
j j 1
j j
>
j j 1
+
j j
j j 1
j j 2
: Then
v
0 and
reveals full
for all v su¢ ciently high.
The …rst part of this Corollary shows that full information for the lowest type
1
is optimal
for high v: It is an informational analogue of the “no distortion at the top” result from the
mechanism design literature (see, e.g. Mirrlees (1971)). In the mechanism design version of
our environment, the incentive constraints bind upward, so that
that no other type wants to pretend to be
1:
1
is the “top type”in a sense
This property of the top types drives both the
“no distortion at the top” result in standard mechanism design models with commitment and
part 1 of Corollary 2 in our environment.
Part 2 of Corollary 2 shows that informational distortions are suboptimal for the highest
j j
as long as the types are not too close to each other. The extra condition is needed to
22
rule out bunching. When some types are close, it might be optimal to give them the same
allocations even if they reveal their type fully (as, for example, in models with commitment)
in order to provide incentives for other types. Since bunching is suboptimal with two types,
no additional conditions were necessary in Theorem 2.
More insight into the behavior of the interior types can be gained from assuming that the
utility function satis…es U (c) = ac1=a for a > 1: In this case it is easy to …nd the limiting
allocations towards (uv ; wv ;
v)
converge as v ! v: In particular, we can use homogeneity of
C and boundedness from below of u to show that for any v; kt (v0 v) =v a ! k~t (v) as v0 ! v;
where function k~t (v) is de…ned by
h
i
^
k~t (v) =
max
E
(32)
t C (u) + t+1 kt+1 (w)
fu(m);w(m); (mj )gm2M
( j )2 (M )
subject to (22) and (21). Moreover,
v
converges to a solution ~ of this problem.
The limiting problem (32) has no cost of information revelation. It is equivalent to a
standard mechanism design problem in which agents can send reports over a redundantly large
message set M : If it is suboptimal to bunch di¤erent types when agents report over
, it
is also suboptimal to bunch types when agents report over M : A su¢ cient condition to rule
out bunching in mechanism design problems is an assumption that types are not too close,
which we state as Assumption 2. It turns out to be a su¢ cient condition for full information
revelation for high enough v in our economy without commitment.
Assumption 2 The distribution of
(
n 1) [ n
n 1]
satis…es
(
n 1
n 2)
j j
X
( i)
0 for all n > 2:
(33)
i=n 1
Note that this assumption is satis…ed both in Theorem 1 and Corollary 2. Suboptimality of
bunching in the limit implies that information revelation is suboptimal for all su¢ ciently high
v: The proof of this result is a tedious but mostly straightforward application of the Theorem
of Maximum and we leave it for the Supplementary material.
Proposition 4 Suppose that U (c) = ac1=a for a > 1 and Assumption 2 is satis…ed. Then
there exists vt+ < v such that for all v
vt+ ;
v
reveals full information about each type.
Remember that we take the distribution of initial promises as given. The following lemma
then shows that, depending on the initial utility he will be allocated by the government, an
agent can remain in the no-information region or in the full-information region for an arbitrary
long time.
23
Lemma 3 (i) Assume utility is bounded below by 0. For any T > 0, there exists v0
that
vt
1 ;t
0 such
( jz; ) is uninformative for all (z; ) for t = 1; :::; T . Suppose that the sustainability
constraint (10) binds in periods t = 0; :::; T + 1, then v0 can be chosen strictly greater than 0.
(ii) Suppose the assumptions of Theorem 1 (Corollary 2) are satis…ed, then for any T > 0
there exists v0 > v0+ such that
and
5
j j)
vt
1 ;t
( jz; ) reveals full information about each type (types
1
with positive probability for t = 1; :::; T .
Extensions
We discussion two extensions of the baseline analysis.
5.1
Invariant distribution
In the previous sections we used arbitrary distributions of initial lifetime utilities
: In this
section we brie‡y discuss two implications for our analysis if
is an invariant distribution.
^
^
In this case multipliers ; and do not depend on t, with > ; > 0 needed to prevent
immiseration.12
One implication of the invariant distribution is that no agent is stuck forever in the region
in which no information is revealed. To see this, note that equation (29) shows that agent’s
promised utility strictly increases with positive probability if vt < v and strictly decreases with
positive probability if vt > v ; where v is given by k 0 (v ) = 0: Suppose there is no information
revelation for all v
v + a where a
0: Then the invariant distribution must assign all
the mass to v and, moreover, no information about agents is revealed. But in this case the
sustainability constraint is slack, which is a contradiction. Therefore the “no information”
region lies strictly below v .
Another implication of Theorem 1 and bounds (29) in this case is that there must exist
an endogenous lower bound beyond which agents’lifetime utility never falls. Once an agent’s
utility reaches that bound, he bounces from it with a positive probability. This dynamics
resembles that of Atkeson and Lucas (1995), except that in their case the utility bound was set
exogenously. Near the endogenous lower bound agent may reveal no information and receive
no insurance against that period’s shocks.
For given ^ ; ; one can follow the arguments of Farhi and Werning (2007) to show that there exists initial
distibution ~ with a property that t generated by a solution to (20) is such that t = ~ for all t: This
distribution is invariant if feasibility and sustainabilty constraints hold with equalities. We leave it for future
research to explore under which conditions these constraints are satis…ed.
12
24
5.2
Persistent shocks
We chose to focus on iid shocks in our benchmark analysis. Most of our key results extend
with few modi…cations to Markov shocks. When the shocks are Markov, let
the probability of realization of shock
assume that
j
> 0 for all ;
conditional on shock
conditional on shock
t
: Let
j
denote
in the previous period. We
be the probability of realization of
j
being realized t periods ago.
Many arguments in the persistent case are straightforward extentions of our previous analysis. We brie‡y sketch them in this section leaving the details for the Supplementary material.
Following the same steps as before, we can show that in the worst equilibrium there is no
information revelation for the government. The payo¤ in that equilibrium, unlike the iid case,
depends on the prior beliefs that the government has. The maximum payo¤ that the government can achieve in any period t is given by
Z
~
Wt ( t ) =
sup
fut+s (h)gh2H t ;s
0
Ht
1
X
s
s=0
Ept+s [ jh] ut+s (h) d
t
subject to the feasibility constraint (8) holding for all t + s and
Z
s
pt+s jht =
j
pt d jht for s > 0:
~ t ( t ) with a function that is linear in
Similarly to the iid case, we can bound W
t 1:
De…ne
the analogue of (13) as
Wt ( ; p) =
max
fut+s (m)gs
0
Mt
Z
1
X
s=0
0
s@
Z
s
(d s j )
s ut+s (m)
w
t;t+s (C
(ut+s (m))
1
e)A (dmj )
d j
then Lemma 2, and in particular bound (14), can be extended to Wt ( t ; pt ) : It is straightforward then to obtain the analogue of Lagrangian (17). This Lagrangian can then be rewritten recursively using the techniques of Fernandes and Phelan (2000), who studied an economy with persistent shocks and commitment.
v= v
period,
1
; :::; v
j j
In their formulation the state is a vector
of promised utilities and the realization of the shock in the previous
: In our environment v remains a state variable with an analogue of the promise
keeping constraints (21) holding for each type,
Z
v i = [ u (m; z) + w (m; z; )] (dmjz; ) dz
d j
i
E
u + wj
i
.
(34)
In the environments with commitment each agent plays a pure reporting strategy and
is known along the equilibrium path. In our settings
25
is not known, but the planner forms
p d
;
posterior beliefs about
: Therefore, the only di¤erence from the commitment environment
is that the posterior belief p replaces
as the state variable.
The recursive formulation is given by
kt (v; p) =
max
(u;w; )
( j )2 (M );p0 2 ( )
X
p
2
E
h
u
t
C (u) + ^
t+1 kt+1
i
0
w; p j
t
Z
Wt dz
(35)
subject to (34), the incentive constraint
E [ u + w ( ; ; ) j ; z]
E 0 [ u + w ( ; ; ) j ; z] for all z; ;
0
;
and the Bayes rule condition that requires p0 to satisfy, whenever de…ned,13
P
(mj
)
j
p
2
p0 ( jm; z) = P
:
j
p
( ; )2 2 (mj )
The analysis of dynamic mechanism design problems with persistent shocks is more involved
since the recursive problem with additional state variables is more complicated. The broad
lessons about desirability of information revelation for high and low promised values (now
in the sense of increasing each element of vector v) still holds. First of all, the example in
Section 4.1 remains virtually unchanged. More speci…cally, in the Supplementary material we
follow similar steps as in the iid case and de…ne functions
1 (v; p)
that both these functions are homogenous in v: for any x > 0;
0 (xv;
) = xa
0 (v;
). Note that v
and
1 (xv)
0 (v;
=
) : We show
xa
1 (v; p)
and
0 if 1=a 2 (0; 1) and v < 0 if 1=a < 0: We can
then conclude that no information revelation is optimal for low values of xv (i.e. x ! 0 if
1=a 2 [0; 1) and x ! 1 if 1=a < 0) and, when no bunching is desirable with commitment,
full information is optimal for high values of xv. We can also generalize Theorem 1 to the
persistent case (see the Supplementary material for details).
Proposition 5 Suppose that utility is bounded. Let
v;p
be a solution to (35) and
mative strategy. If the sustainability constraint (10) binds in periods t; then Pr (
as v ! 0 for all p.
6
an uninforv;p
! )!1
Final remarks
In this paper we took a step towards developing of theory of social insurance in a setting in
which the principal cannot commit. We focused on the simplest version of no commitment
13
Strictly speaking m should be replaces with any Borel set A of
26
(Mt ) analogously to de…nition (3).
that involves a direct, one-shot communication between the principal and agents, and showed
how such model can be incorporated into the standard recursive contracting framework with
relatively few modi…cations. Our approach can be extended to other types of communication. For example, a literature starting with a seminar work of Myerson (1982) considered
communication protocols that involve a mediator. Such protocols may further increase welfare (see, e.g. Bester and Strausz (2007)) but they require some ability to commit by the
policy maker to use the mediating device. The key di¤erence is that, after sending any message m; the agent receives a stochastic allocation, so that the incentive constraint (25) holds
in expectation rather than message-by-message. Two main insights of the paper – recursive
characterization and Theorems 1 and Theorems 2 –depend little on the detailed structure of
the incentive constraints. We believe that our analysis can be extended to such settings in a
relatively straightforward way and leave it to future research.
Another important direction that needs to be explored in future work is how the allocations
in best equilibria can be decentralized through a system of taxes and transfers. Some of the
most fruitful way to proceed may be to extend our basic set up to incorporate such margins as
labor supply or job search e¤ort, and consider decentralizations along the lines of labor taxation
in Albanesi and Sleet (2006) and unemployment insurance in Atkeson and Lucas (1995).
27
7
Appendix
7.1
Proof of Lemma 2
w
t gt
First we show that sequences f
is uniformly bounded away from 0. The objective function
w
t
in (7) is concave and the constraint set is convex, therefore there exists
t
solution to (7), uw
t h
w
t
ht 2H t
is given by
t
; satis…es C 0 uw
t h
Z
C C0
1
1
wE
t
Ht
Since E t [ jh] 2
in…nity as
w
t
1; j j
t
1
=
E
w
t
[ jh]
d
jht : The Lagrange multiplier
t
t
= e:
(36)
; the left hand side of (36) is continuous in
w
t
goes in…nity and 0 respectively. Therefore
0 such that the
w
t
and goes to 0 and
is bounded away from 0 from below
and bounded above, and these bounds can be chosen independently of t. This also implies that
the supremum to (7) is obtained. The same arguments applied to (13) establish that Wt is
well de…ned, uw (m) satis…es
1
C 0 (uw (m)) =
1
w;
t
[ jm] 2
wE
t
j j
w
t
;
(37)
and the family fWt gt is uniformly bounded. To see that Wt is convex, for any
2 [0; 1] ;
0
Wt
+ (1
00
)
=
Z
max
fu(m)gm2M
Mt
t
+ (1
)
Z
max
fu(m)gm2M
=
0
Wt
Z
max
fu(m)gm2M
+ (1
t
Z
) Wt
(u(m))]
(u(m))]
w
t C
[ u (m)
Mt
t
)
w
t C
[ u (m)
Mt
+ (1
w
t C
[ u (m)
w
t C
0
00
and
(dmj ) (d )
(dmj ) (d ) +
(u(m))]
[ u (m)
Mt
00
00
0
0;
w
t e
(dmj ) (d )
(u(m))]
00
(dmj ) (d ) +
:
To see that Wt is minimized if and only if a strategy is uninformative, consider any uninformative . From (37), the solution to (13) given
Wt ( ) = C 0
w
t C
1
1
w
t
C0
1
1
w
t
: Let
message set M and note that for any
Wt ( )
=
max
Wt ( )
Z
fu(m)gm2M
t
=
max
fu(m)gm2M
t
Mt
Z
Mt
[( u (m)
w
t C
f(E [ jm] u (m)
(u (m)))
w
t C
1
satis…es C 0 (uw
a.s. and hence
t (m)) = w
t
R
(A) =
(Aj ) (d ) for any Borel A of
( uw
t
(u (m)))
28
w
t C
(uw
t ))] (dmj ) (d )
(E [ jm] uw
t
w
t C
(uw
t ))g (dm) :
w
t e
The expression in curly bracket is non-negative, which implies that Wt ( )
all
: Moreover for informative
jE [ jA]
, there is a set of messages A with
Wt ( ) for
(A) > 0 such that
1j > 0: For all such messages the expression in curly brackets is strictly positive
since uw
t does not satisfy the optimality condition (37) for m 2 A: Since
expression above is strictly positive therefore any informative
(A) > 0; the
cannot be a minimum.
We prove (15) by using Theorem 3 in Milgrom and Segal (2002). For completeness, we
state it here adapted to our set up
Theorem 3 Let V (t) = supx2X f (x; t) where t 2 [0; 1] ; and let x (t) be a solution to this
problem given t and ft be the derivative of f with respect to t: Suppose that (i) for any t
a solution x (t) exists, (ii) fft (x; )gx2X is equicontinuous, (iii) supx2X jf (x; t) j < 1 at
t = t0 , and (iv) ft (x (t) ; t0 ) is continuous in t at t = t0 : Then V 0 (t0 ) exists and V 0 (t0 ) =
ft (x (t0 ) ; t0 ) :
In our case,
f (fug ; ) =
Z
( u (m)
Mt
w
t C
(u (m))) (1
can be maximized pointwise. For each m,
Z
w
( u (m)
t C (u (m))) (1
0
) (dmj ) +
) (mj ) +
0
(mj )
(dmj )
(d )
(d )
is continuous is u (m) and by (37) the latter can be restricted to a compact set, hence conditions
(i) and (iii) of this theorem are satis…ed. The solution, given by (37), is integrable and, thus,
so is the continuous and bounded transformation uw (m)
w
t C
Theorem 11.18 and Remark 11.23.) The derivative with respect to
Z
w
0
f (fug ; )
( u (m)
(dmj )
t C (u (m)))
(uw (m)) (Rudin (1976),
is
(dmj )
(d ) ;
Mt
and it does not depend on , therefore ff (fug ; )gfug is equicontinuous. Also, if either
R
R 0
(mj ) (d ) > 0 or
(mj ) (d ) > 0 for some m, the solution uw
t (m; ) is unique for
2 (0; 1) and, by the Theorem of the Maximum, there is a solution that is continuous in for
R
R 0
2 [0; 1]. Finally, if
(mj ) (d ) =
(mj ) (d ) = 0 for some m, we can always …nd
a solution uw
t (m; ) that is continuous in
for
2 [0; 1]. Since uw
t (m; ) is continuous in
for all m 2 Mt , we can use the dominated convergence theorem to show that f (fu ( )g ;
is continuous in
at
=
0;
0)
which veri…es condition (iv).
Since the sequence f t gt is uniformly bounded (away from zero from below), equation (37)
implies that uw
t (m) is bounded and those bounds do not depend on t: Therefore all the families
of directional derivatives f@Wt ( ) =@ 0 gt are uniformly bounded.
29
We prove (14) next. By Lagrange Duality theorem (Luenberger (1969), Theorem 1, p.
~ t ( t ) can be written as a minmax problem
224), W
Z
~
Wt ( t ) = min max
(E t [ jh] u (h)
C (u (h))) d t + e
0 fu(h)gh2H t H t
Z
w
w
max
(E t [ jh] u (h)
t C (u (h))) d t + t e
fu(h)gh2H t
=
=
max
fu(h)gh2H t
Z
Ht
Z
Wt
Ht 1
Ht
t
Z
1
Mt
jht
1
n
;
u ht
dzd
1
By de…nition of
u(ht
1
; m)
o
t
mjht
1
;
dm (d ) dzd
t 1:
where the inequality follows from the fact that
w
t
w
t C
;m
w
t
may not be a minimizer for an arbitrary
this inequality becomes equality at
t;
t:
which establishes (14).
Finally, if we can restrict Mt to be …nite (as proved in Proposition 3) then Wt ( ) is
continuous in . This is immediate as we can restrict fu (m)g to lie in a compact subset of
RjMt j and use the Theorem of the Maximum.
7.2
Proof of Proposition 3
First we prove some preliminary results. Fix z and consider any incentive compatible allocation
that satis…es (22). Let Mt ( ) be as de…ned in the text. For any i let Mt ( i ) = Mt ( i ) \
Mt (
i 1 ),
Mt+ ( i ) = Mt ( i ) \ Mt (
i+1 )
and Mtexcl ( i ) = Mt ( i ) n ([j6=i Mt ( j )) :
Lemma 4 For all i; Mt ( i ) = Mt ( i ) [ Mtexcl ( i ) [ Mt+ ( i ) :
Proof. Suppose m 2 Mt ( i ) nMtexcl ( i ) : Then there exists j such that m 2 Mt ( j ) :
Without loss of generality let
i+1 u
j
>
i:
For any m0 2 Mt (
m0 + w m0
i+1 )
i+1 u (m)
+ w (m)
and
i u (m)
+ w (m)
iu
m0 + w m0 ;
j u (m)
+ w (m)
ju
m0 + w m0 :
The sum of the …rst the second inequalities implies u (m0 )
the third inequalities implies u (m0 )
Lemma 5 Let (u ; w ;
u (m), the sum of the …rst and
u (m) ; therefore u (m0 ) = u (m) and m 2 Mt (
i+1 ) :
) be a solution to (20) for a given z: Then (u (m0 ) ; w (m0 )) =
(u (m00 ) ; w (m00 )) for all m0 ; m00 2 Mt ( t ) ; for all m0 ; m00 2 Mt+ ( t ) and for almost all (with
respect to measure
) m0 ; m00 2 Mtexcl ( i ) :
30
t 1
Proof. The …rst part of the lemma follows immediately from the discussion in the text, so
u (m) jm 2 Mtexcl ( ) ; w
^=E
we prove the second part. Let u
^=E
and consider an alternative (u0 ; w0 ;
) de…ned as (u0 (m) ; w0 (m)) = (u (m) ; w (m)) if m 2
=
Mtexcl ( ) ; and (u0 (m) ; w0 (m)) = (^
u; w)
^ if m 2 Mtexcl ( ) : For any
0
therefore
0
u
m0 + w
m0 >
0
u (m0 ) + w (m0 ) >
w (m) jm 2 Mtexcl ( )
0
0
6= ; m0 2 Mt
0
u (m) + w (m) for all m 2 Mtexcl ( ) ;
u
^ + w,
^ which implies that (u0 ; w0 ;
) satis…es (22). It
also satis…es (21) by construction, since
m 2
Mtexcl
gets the same utility from reporting any message
h
i
^ kt+1 (w) is strictly concave
( ) : The objective function E
u
C
(u)
+
t
t+1
in (u; w) ; and would take a strictly higher value at (u0 ; w0 ) than at (u ; w ) unless (u ; w ) is
constant on Mtexcl ( i ) a.s.
Lemma 6 Let (u ; w ; ) be a solution to (20) for a given z: Suppose there exists a set
P
~j
~
M
( ) > 0 and u (m0 ) = u (m00 ) for almost all (with respect to
M
Mt s.t.
~ . If t > 0 then E [ jm0 ] = E [ jm00 ] a.s:
measure ) m0 ; m00 2 M
~ and consider an alternative strategy 0 de…ned as 0 (mj ) =
Proof. Fix any m
^ 2 M
~ and 0 (mj
~j
(mj ) if m 2
= M
^ ) =
M
for all : Any agent reports any subset of
messages with a positive probability with reporting strategy
with a positive probability with
0
: Therefore the strategy pro…le
2 [0; 1]. Let
h
fm
E
u
^ ( )
only if he reports that subset
= (1
)
t Wt (
):
+
0
satis…es
(21) and (22) for any
^
t C (u ) + t+1 kt+1 (w )
Since u (m0 ) = u (m00 ) ; w (m0 ) = w (m00 ) ;
0
fm
^ ( )j
=0
=
=
i
@Wt ( )
@
w
w
~)
f(E 0 [ jm]
^ uw (m)
^
^
Pr(m 2 M
t C(u (m)))
Zt
w
w
( uw (m)
t C(u (m))) (mj )dm (d )g:
t
~
M
0 ( )j
Optimality of
= 0 implies that fm
^
h
i
w
w
~ uw (m)
E
jM
^
^
E
t C (u (m))
0 for all m;
^ so that it can be written as
h
i
w
w
~
E [ jm] uw (m)
^
t C(u (m))jM all m:
=0
~ of both sides, we obtain E
Taking expectations conditional on M
h
i
~ which implies that cov (E [ jm] ; uw (m))
E [ jm] uw (m)jM
E
optimality (37) implies that
uw
h
(m) is monotonically increasing in E
31
i
~
jM E
h
~
uw (m)j
^ M
i
0: On the other hand,
[ jm] ; and therefore
cov (E
a.s.
[ jm] ; uw (m))
0: The two conditions can be satis…ed only if E
Proof of Proposition 3 and Corollary 1.
any solution to (20) can take at most 2j j
[ jm0 ] = E
Lemmas 5 and 6 show that for a given z;
1 distinct values of (u (m) ; w (m) ; E
except for possible values that occur with probability 0 under reporting strategy
6 is stated for the case
t
> 0; but when
t
[ jm00 ]
[ jm])
(Lemma
= 0 the problem is isomorphic to the standard
mechanism design problem and usual arguments apply to show that j j distinct allocations
represent a solution). The outcomes that occur with probability zero can be replaced with any
outcome from that set of 2j j
1 distinct values. Therefore without loss of generality the set
M can be restricted to at most 2j j
1 messages in (20), and hence, by Proposition 2, to M
in the modi…ed problem (17).
It remains to verify that it is a best equilibrium since not every solution to (17) needs to be
a PBE. Let (
;
G; p
) be a best PBE that generates (u ; M ) along the equilibrium path.
By the arguments leading to construction of problem (17), (u ;
) is a solution to that prob-
lem given M : It is easy to show that any equilibrium is payo¤-equivalent to one in which the
P1 s t
us jht 1
E
allocations in period t depends only on the expected utility wt ht 1
s=t
but not on the particular realizations of shocks in the previous t
the Supplementary materials) and so we assume that (u ;
1 periods (Lemma 10 in
) satis…es this property. Pre-
vious arguments imply that after any history ht there can be at most 2j j 1 distinct
n
h
i o
values of
ut ht ; mt ; wt ht ; mt ; E
jht ; mt
that occur with probability 1 given
mt
o
n
jht ;
: Therefore it is possible to construct another strategy 0 which is incentive
t
2
compatible and delivers the same payo¤ to the agents as
tribution of histories
any Borel set A of
0
with a property that Pr
([(1
) v; (1
E C (ut ) ; which veri…es that ( 0 ;
) v]
G; p
G)
generates a dis-
2 A) = Pr ((ut ; E t ) 2 A) for
~ t ( ) and E 0 C (ut ) =
~ t ( 0t ) = W
) : Therefore W
t
0
((ut ; E
: The pair ( 0 ;
t)
) is a best PBE and proves Proposition 3.
If removing all non-distinct messages leaves fewer than jM j messages, extra messages can
be added and agents strategies extended to keep posterior probabilities for such messages the
same as for some of the original messages. By appropriately choosing which messages to add it
is possible construct strategies that satisfy (25). This argument extends for all histories, and
hence any value that k0 (v) achieves given any M; can also be achieved given Mt = M for all
t: This completes the proof of Corollary 1.
32
7.3
Proofs for Section 4
First, we use Proposition 3 to simplify our problem. We drop explicit dependence of all
variables on z and throughout this section all the results are understood to hold for all z: By
Proposition 3 we can restrict attention to messages in a set Mv of cardinality no greater than
2j j
1 such that no two distinct reports give the agent the same allocation. We use Nv to
denote cardinality of Mv and Mv ( ) to denote the set of messages in Mv that maximize agent
’s utility. The incentive constraints (22) can be written as
u m0 + w m0 ;
u (m ) + w (m )
m0 j
u m0 + w m0
( u (m ) + w (m ))
The triple (uv ; wv ;
=0 8
is a solution to
h
^
max E (1
v) u
t C (u) + t+1 kt+1 (w)
(38)
; m 2 Mv ( ) ; m0 2 Mv :
2
v)
v
u;w;
subject to (38) where
v
w
i
t Wt (
)
(39)
= kt0 (v) :14 Without loss of generality we arrange messages in Mv
so that uv (m1 ) < ::: < uv (mNv ) ; which also implies that wv (m1 ) > ::: > wv (mNv ) : Let
0
( ; m ; m0 ) and
00
( ; m ; m0 ) be Lagrange multipliers on the …rst and second constraint
(38). We set ( ; m; m0 ) = 0 for all m 2
= Mv ( ) and ( ; m; m) = 0 for all m; so that
0
;
00
are
well de…ned for all ( ; m; m0 ) :
The next lemma establishes bounds on optimal allocations that are important for establishing our main results in this section.
Lemma 7 (uv ; wv ;
(29) hold, with % =
v)
satis…es (26): For all v such that kt0 (v)
1+
^
j j
1
t+1
1
;%=
j j +1
1
^
t+1
j j
:
Proof. The …rst order conditions for wv (m) are
"
#
X ^ t+1
X
0
kt+1
(wv (m))
v (mj ) ( )+
v
2
X
( ;m0 )2
Sum over m to obtain
X
( ;m)2
Mv
"
^
( ;m0 )2
0
t+1 0
kt+1 (wv
0
#
(m))
v
; m; m0 +
v
(mj )
00
; m; m0
Mv
; m0 ; m +
Mv
1, equations (27), (28) and
v
m0 j
(mj ) ( ) =
v
0
; m0 ; m
= 0: (40)
= k 0 (v) ;
14
To see this, let v be the Lagrange multiplier on the promise keeping constraint in the original, convexi…ed
Bellman equation. By Proposition 1 and the envelope theorem it satis…es v = kt0 (v) : Form a Lagrangian with
v and observe that it can be maximized for each z separately, which yields (39).
33
which is expression (26).
For what follows, it is useful to establish bounds on the Lagrange multipliers. Consider
0
a message m1 : If Nv = 1; then trivially
Nv > 1 and let
0
be the largest
strictly suboptimal for any
with
0
>
0
: Moreover,
0
>
0
;
00
and
are two scalars equal to zero. Suppose
such that m1 2 Mv ( ) : Since sending message m1 is
( ; m0 ; m1 ) =
0
uv (m1 ) + wv (m1 )
v
(m1 j )
00
( ; m0 ; m1 ) = 0 for all ( ; m0 )
uv (m) + wv (m) and uv (m1 ) < uv (m) for
all m 6= m1 ; which implies u (m1 ) + w (m1 ) > u (m) + w (m) for all m 6= m1 if
Therefore,
0
( ; m1 ; m0 ) =
v
write (40) for m1 as
(m0 j )
^
00
( ; m1 ; m0 ) = 0 for all ( ; m0 ) with
t+1 0
kt+1 (wv
(m1 ))
v
!
0
<
<
0
:
: Thus we can
= # (m1 ) ;
(41)
where
# (m1 ) =
P
m0 2Mv
0
0
; m1 ; m0 +
m0 j
v
0
00
0
0
0
; m1 ; m0
; m0 ; m1 +
P
v (m1 j ) ( )
2
Since w is decreasing in m and kt+1 is concave,
v;
^
t+1
^
0
kt+1
(wv (m1 ))
t+1
E
v
v
m1 j
0
00
0
0
kt+1
(wv ) =
which implies that
# (m1 )
Similar steps for mNv establish # (mNv )
0:
(42)
0:
The …rst order conditions for uv (m) are
X
(1
v)
tC
0
(uv (m))
2
X
( ;m0 )2
where (m)
v
(mj ) ( )+
X
( ;m0 )2
0
; m0 ; m +
Mv
v
0
; m; m0 +
v
00
(mj )
; m; m0
Mv
m0 j
00
; m0 ; m
0 is the Lagrange multipliers on the constraint u (m)
=
(m) ; (43)
U (0) : It is zero if utility
is unbounded below. Moreover, since we assumed uv (m1 ) < ::: < uv (mNv ) ; it can only be
strictly positive for m1 even in the case when utility is bounded below.
We guess and verify that if kt0 (v) =
v
1; then
(m1 ) = 0:15 Suppose v (m1 ) = 0: Then
the …rst order condition for uv (m1 ) becomes
X
(1
v)
tC
0
(uv (m1 ))
2
15
More precisely, for a …xed
su¢ cient.
v;
v
(m1 j ) ( ) = # (m1 )
X
2
v
!
(m1 j ) ( )
0
:
(44)
maximization problem (39) is convex and thus necessary conditions are also
34
; m0 ; m1
:
Combining it with (42), it implies that
tC
0
(uv (m1 ))
(1
v) E
[ jm1 ]
v
0
and veri…es that the lower bound for uv (m1 ) does not bind. Analogous arguments establish
(1
v) E
[ jmNv ]
v
tC
0
(uv (mNv )) ;
which, together with the monotonicity assumption on uv (m) ; gives (28).
For the rest of the proof consider v that satis…es kt0 (v)
1: Summing (43) over m when
(m) = 0 implies (27). Finally, combining (41) with (44) we obtain
^
t+1 0
kt+1 (wv
(m1 )) =
v
+
v
+
1
1
1
tC
0 (u
v
(m1 ))
v
tE
v
0
0
where we used
v
0
v
(
E
v
[ jm1 ]
E
v
[ jm1 ]
1) +
1
1
0
1
0
+
+
1
1
0
tC
0
(uv (m1 ))
1
0 v
v;
[C 0 (uv )] = 1
v
to get the second inequality. Re-
arrange it to get
1
0
kt+1
(wv
0
(m1 ))
^
^
1
0
t+1
+1
1
j j
(1
+1
v)
(1
v)
1
t+1
+
1
+
^
1
t+1
^
!
t+1
!
:
This, together with monotonicity of wv (m) ; establishes the upper bound in (29). Analogous
manipulation of the …rst order condition for mNv establishes the lower bound in (29).
Finally, note that
%
and
%
1
j j
^
t+1
+1
! 0 as
j j
^
=
t+1
^
! 0 as
1
1
1
j j
1
j j
1
t+1
j j
+1
1
1
+1
1
1
! 0 since we assume that E [ ] = 1. Therefore,
! 0. Analogous arguments prove that %
^
t+1
! 0 as
j j
1
! 0.
We use this lemma to establish bounds that we use to characterize information revelation
for low v:
35
Lemma 8 (a) If utility is unbounded below and constraint (10) binds in period t+1; then there
are scalars Au;t > 0; Aw;t > 0 and vt such that for all v
vt any solution to (39) satis…es
0
uv (m)
uv m0
Au;t for all m; m0 ;
0
wv (m)
wv m0
Aw;t for all m; m0 :
(b) If utility is bounded below, without loss of generality by zero, then limv!v uv (m) = 0
and limv!v wv (m) = 0 for all m:
Proof. (a) When (10) binds in t + 1; ^ t+1 >
is unbounded below,
limv! 1 kt0 (v)
vt such that
1
2
1
^
t+1
!
1
^
> 0: When utility
t+1
= 1 and therefore expression (29) implies that there exists
0
kt+1
(wv
1
and therefore
3
2
(m))
1
^
t+1
!
for all m; v
vt :
This establishes bounds for wv (m) : The incentive constraint
1 uv
(m1 ) + wv (m1 )
1 uv
(mNv ) + wv (mNv )
together with monotonicity wv (m1 ) > ::: > wv (mNv ) ; uv (m1 ) < ::: < uv (mNv ) imply that
(wv (m1 )
w (mNv ))
1
uv (mNv )
uv (m1 )
0
establishing bounds for uv :
(b) When utility is bounded, Proposition 1 shows that limv!v kt0 (v) = 1: For any
the largest v that satisfy kt0 (v )
close to v = 0: Let v~ = E
v
: By choosing arbitrarily high
we can set v arbitrarily
[ uv + wv ] : Due to the possibility of randomization, in general
v ) : Therefore v~
v~ 6= v but kt0 (v) = kt0 (~
v
…nd
v~ = E
E
v
v
if v
v : Then
[ uv + wv ]
(45)
[ 1 uv + wv ]
X
( 1)
(mj 1 ) [ 1 uv (m) + wv (m)]
v
m2Mv (
1)
( 1 ) [ 1 uv (m1 ) + wv (m1 )]
( 1 ) wv (m1 )
0:
Here the second, third and …fth lines follows from nonnegativity of u and w; and the fourth
line follows from the fact that if
1
(mj 1 ) > 0; then (uv (m) ; wv (m)) gives the same utility to
as (uv (m1 ) ; wv (m1 )) : Since v
limv!v wv (m1 ) = 0: Since wv (m1 )
can be chosen to be arbitrarily close to 0, this implies that
wv (m) ; this implies that limv!v wv (m) = 0 for all m:
Analogous arguments show that limv!v uv (m) = 0:
36
7.3.1
Proofs for low v
We now can prove the …rst limiting result about optimal information revelation.
Lemma 9 Suppose that sustainability constraint (10) binds in periods t and t + 1. Then
v
converges to an uninformed strategy as v ! v:
Proof. Let
be any uninformative strategy. Let uv (m) = E
uv ; wv (m) = E v wv for
v
all m: Note that since uv (m) is increasing in m
uv (m1 ) = uv (m1 ) E
uv (m)
v
uv mj
j
E
v
= uv mj
j
;
and an analogues relationship holds for wv :
Pro…le (uv ; wv ; ) is incentive compatible and satis…es
E
v
[ uv + wv ] = E [ uv + wv ] :
The value of the objective function (39) evaluated as (uv ; wv ;
v)
(46)
should be higher than eval-
uated at (uv ; wv ; ) ;
E
v
h
uv
uv
tC
tC
(uv ) + ^ t+1 kt+1 (wv )
(uv ) + ^ t+1 kt+1 (wv )
t Wt ( v )
t Wt (
):
i
(47)
First, suppose that utility is bounded below, without loss of generality by zero. From
Lemma 8, uv (m) ! 0 and wv (m) ! 0 for any m as v ! 0; and therefore uv and wv also
converge to zero. Hence in the limit equation (47) becomes
lim sup
v!v
Since Wt (
v)
t (Wt (
Wt ( ) by Lemma 2 and
exists and satis…es limv!v Wt (
v)
t
)
Wt (
v ))
0:
(48)
> 0 when (10) binds in periods t, limv!v Wt (
= Wt ( ) : Wt ( ) is continuous in
v)
and achieves its mini-
mum only at uninformative reporting strategies by Lemma 2, therefore
v
must converge to
some uninformative strategy.
Now suppose that utility is unbounded below. By the mean value theorem
t (C
^
(uv (m))
t+1 (kt+1 (wv )
C (uv )) =
tC
0
(~
uv (m)) (uv (m)
uv ) ;
0
kt+1 (wv )) = ^ t+1 kt+1
(w
~v (m)) (wv (m)
wv ) ;
for some u
~v (m) that takes values between uv (m) and uv and for some w
~v (m) that takes
values between wv (m) and wv : By construction, uv (m1 )
37
uv
uv (mNv ) and wv (m1 )
wv
wv (mNv ), therefore, uv (m1 )
From (28) and (29) limv!
1C
w
~v (m)
0 (~
uv
uv (mNv ) and wv (m1 )
(m)) = 0 and limv!
w
~v (m) wv (mNv ).
0
~v (m)) = = ^ t+1 for all m:
1 kt+1 (w
We have
lim E
v
lim E
v
v! 1
=
v! 1
= 0;
h
(uv
h
tC
uv )
0
t (C
0
uv ) + ^ t+1 kt+1
(w
~v )
(~
uv ) (uv
i
kt+1 (wv ))
i
wv )
C (uv )) + ^ t+1 (kt+1 (wv )
(uv )
(wv
where the second line uses the mean value theorem and (46), and the last line uses the fact
that (uv (m)
uv ) and (wv (m)
wv ) are bounded for low v by Lemma 8. This implies that
(48) holds when utility is unbounded and that
v
converges to an uninformative strategy.
We now can prove Theorem 1.
Proof of Theorem 1. Suppose Nv > 1 for some realization of z and consider (uv ; wv ;
that solve (39) for such z: Let
allocation when priors
Wt (
=
v)
max
+
[E
m m2
: Let uw be the optimal
w
t C
[( u (m)
( uw
(u (m)))
w
t C
(uw ))]
v
(mj ) ( )
m; 2Mv
8
<
=
max
[E
fu(m)gm2Mv :
X
0
v
be the largest such that m1 2 Mv
are uninformative: Then
Wt ( )
X
fu(m)gm2Mv
0
v
v
v)
v
w
t C
[ jm1 ] u (m1 )
[ jm] u (m)
w
t C
(u (m1 ))
(u (m))
(E
v
(E
v
[ jm1 ] uw
[ jm] uw
w
t C
w
t C
0
(uw ))] @
0
(uw ))] @
X
0
v
X
0
v
v
(m1 j ) ( )A
19
=
A
(mj
)
(
)
v
;
All terms in square brackets are non-negative since the choice u (m) = uw is feasible. They
are strictly positive if E
v
[ jm] 6= 1; since uw is the optimal allocation for E [ jm] = 1: From
Lemma 9 the left hand side of this expression goes to zero as v ! v; therefore the right hand side
should also go to zero. This is possible either if (a) E v [ jm1 ] ! 1 (and hence 0v ! j j ) and
P
P
0
0
v (mj ) ( ) ! 0 for all m > m1 ; or (b)
v (m1 j ) ( ) ! 0; E v [ jm2 ] !
v
v
P
0
1 and
0
v (mj ) ( ) ! 0 for all m > m2 (and hence v ! 1 and m2 2 Mv ( 1 )). The
v
P
other possibilities are ruled out since if E v [ jm] ! 1 and
0
v (mj ) ( ) 9 0 for some
v
P
0
0
m > m2 ; then for some m0 m2 we would have
0
v (m j ) ( ) 9 0 and E v [ jm ] 9
v
1.16 Since it is impossible to have
16
Note that
all m > m2 .
1
j j
and
1
to be indi¤erent between more than two distinct
can be indi¤ererent between at most two distict allocations and therefore
38
v
1
(mj 1 ) = 0 for
allocations in the optimum, for any " > 0 there must be some vt
such that for all v
solution has Nv = 2 and either (a) m1 2 Mv
", E
E
v
E
v
j j
,
v
[ jm1 ] arbitrarily close to 1, or (b) m2 2 Mv ( 1 ) ;
m2 j
v
j j
(m1 j 1 )
v
"; E
[ jm2 ] =
v
0
uw
v (m1 ) ! C
1 (1= w ) ;
t
0
and in case (b) uw
v (m1 ) = C
1(
w
1= t )
j j
[ jm1 ] =
0
[ jm2 ] arbitrarily close to 1. In case (a) (37) implies that uw
v (m2 ) = C
1
and uw
v (m2 ) !
vt the
1
> 1 and
< 1 and
w
and
j j= t
0
1
C (1= w
t ):
We can now rule cases (a) and (b) for v low enough. Consider case (b), case (a) is ruled
out analogously. In this case
v
(30) is
1 (uv
(m2 )
(m1 j 1 ) < 1 for v low enough and the optimality condition
uv (m1 ))
+ ^ t+1 [kt+1 (wv (m2 ))
= [( 1 uw
v (m2 )
Function
1u
w
t C
w
t C
t (C
(uv (m2 ))
C (uv (m1 )))
(49)
kt+1 (wv (m1 ))]
(uw
v (m2 )))
( 1 uw
v (m1 )
w
t C
(uw
v (m1 )))] :
(u) is strictly concave and achieves its maximum u
^ at u
^ = C0
1(
w
1= t )
=
w
w
uw
v (m1 ) : Since uv (m2 ) is bounded away from uv (m1 ) ; the right hand side of (49) is strictly
negative and bounded away from 0.
When utility is bounded below, Lemma 8 established that all terms on the left hand side of
(49) go to zero as v ! v; yielding a contradiction. When utility is unbounded below, substitute
the indi¤erence condition
1 (uv
(m2 )
uv (m1 )) =
(wv (m1 )
wv (m2 )) into (49) and apply
the mean value theorem
t (C
(uv (m2 ))
C (uv (m1 ))) =
tC
0
(~
u) (uv (m2 )
uv (m1 ))
and
^
=
t+1 (kt+1 (wv
^
0
~
t+1 kt+1 (w)
(m2 ))
kt+1 (wv (m1 )))
(wv (m2 )
(wv (m2 )
wv (m1 ))
wv (m1 ))
for some u
~ 2 (uv (m1 ) ; uv (m2 )) and w
~ 2 (wv (m2 ) ; wv (m1 )) : The terms (uv (m2 )
uv (m1 ))
C 0 (~
u)
and (wv (m2 ) wv (m1 )) are bounded for small v by Lemma 8 and limv! 1 t
= 0;
0
(w)
~
= 0 by Lemma 7. Therefore, the left hand side of (49) converges
limv! 1 ^ t+1 kt+1
to zero for utilities unbounded below, yielding a contradiction. This proves that Nv = 1
and
v
is uninformative for all su¢ ciently low v independently of the realization of z: For
uninformative
v;
there is a unique (uv ; wv ) that solves (39) by strict convexity of u
39
tC
(u) :
Proofs for high v
7.3.2
We prove Corollary 2, since Theorem 2 is a special case of it.
Corollary 2. Suppose v is su¢ ciently high so that
case that
1
and
v
= kt0 (v) < 1: We …rst rule out the
send the same message with probability 1 for high v: From (41) and (44)
2
we have that there is #v
0 such that
^
t+1 0
kt+1 (wv
(m1 )) =
#v ;
v
and
tC
where ~ = (
1
and
2
1 1
+
0
(uv (m1 )) = (1
2 2) = ( 1
+
2)
v) E
>
1:
v
[ jm1 ] + #v
(1
v)
~ + #v ;
The last inequality follows from the fact that types
play message m1 with probability 1:
De…ne function f as
f (x)
1 (uv
(m1 )
x)
tC
x) + ^ t+1 kt+1 wv (m1 ) +
(uv (m1 )
This function is concave with
0
f (0) =
tC
1
0
^
(uv (m1 )) +
Let x
^v be a solution to f 0 (^
xv ) = (1
1
v)
t+1 0
kt+1 (wv
~
!
(m1 ))
> (1
v)
1
x :
~
=2 and let (^
uv ; w
^v ) = uv (m1 )
1
1
:
x
^v ; wv (m1 ) +
Since f is concave, x
^v > 0 and u
^v < uv (m1 ) ; w
^v > wv (m1 ) :
Claim 1. Allocation (^
uv ; w
^v ) satis…es bounds (28) and (29).
Let xv be a solution to f 0 (xv ) = 0: By concavity, 0 < x
^v < xv ; so we establish the claim
by proving the stronger statement that uv (m1 )
and (29). By de…nition,
"
1
1
^
t+1 0
kt+1
wv (m1 ) +
xv and wv (m1 ) +
1
#
xv
=
tC
0
1
(uv (m1 )
xv satisfy bounds (28)
xv )
and by xv > 0
tC
^
t+1 0
kt+1
0
(uv (m1 )
wv (m1 ) +
xv ) <
1
tC
^
xv
0
(uv (m1 )) ;
t+1 0
kt+1 (wv
(m1 )) :
These conditions imply that
1 (1
1 (1
v)
v)
tC
1
0
"
(uv (m1 )
^
1
xv ) <
t+1 0
kt+1
j j (1
wv (m1 ) +
40
v) ;
1
xv
#
< (1
v ) j j;
1
x
^v :
establishing the bounds (28) and (29).
Claim 2. (1
^v
v) x
! 1 as v ! v:
In Supplementary material we showed (Lemma 13) that Assumption 1 implies that there
^v such that
are numbers Bv and B
C 0 (uv (m1 ))
0
kt+1
(wv (m1 ))
Bv
2
C 0 (uv (m1 )) x
^v ;
[C 0 (uv (m1 ))]2
^v
B
2
0
kt+1
(w
^v ) x
^v ;
2 1
0
^v )
1 kt+1 (w
C 0 (^
uv )
0
kt+1
(w
^v )
^v = 1
) v; wv (m1 ) ! v then Bv = [C 0 (uv (m1 ))]2 ! 0 and B
and if u
^v ! (1
The bounds from Claim 1 establish that u
^v ! (1
^
t+1
^
0
E v kt+1
(wv )
t+1
(50)
0
kt+1
(w
^v )
2
! 0:
kt0 (v)
) v as v ! v: Since by (27)
=
0
kt+1
(wv (m1 )) ; this implies that wv (m1 ) ! v as v ! v: Therefore by
Lemma 13 the …rst terms on the right hand side of these expression go to zero as v ! v:17
We have
~
1
1
2
1
=
v
1
1
(
f 0 (0)
"
t
v
f 0 (^
xv )
0
C (uv (m1 ))
tC
C 0 (uv (m1 ))
Bv
1
[C 0 (uv (m1 ))]2
v
From Claim 1, both C 0 (uv (m1 )) = (1
v)
0
^
(^
uv ) +
2
+
1
t+1
0
kt+1
(wv
^v
B
1
and 1
1
0
kt+1
(w
^v )
2
0
kt+1
(w
^v ) = (1
0
kt+1
(w
^v )
1
v
v)
^v
v) x
the expression in curly brackets goes to 0 as v ! v: Therefore (1
Claim 3. f (^
xv )
(m1 ))
f (0) ! 1 as v ! v:
0
kt+1
(w
^v )
2
)
(1
#
^v :
v) x
are …nite, therefore
! 1:
Applying the mean value theorem,
f (^
xv )
f (0) =
f 0 (~
xv )
(1
1
v
^v
v) x
for some x
~v 2 (0; x
^v ) : Since f is concave; f 0 (0) > f 0 (~
xv ) > f 0 (^
xv ) : Therefore
h
i
1 ~
~
: The result follows from Claim 2.
1 ;
1
2
We are now ready to show that it is not optimal for types
1
and
2
f (~
xv )
1 v
2
to send the same message
with probability 1 for high enough v: Suppose it is. Consider an alternative strategy ^ v , where
^ v (mj
^ 1 ) = 1 for some message m
^ that gives allocation (^
uv ; w
^v ) ; and ^ v (mj ) =
17
v
(mj ) for
When kt is twice di¤erentiable, this result can be established without using Lemma 13. In this case kt00 (v)
2
2
00
00
0
00
kt0 (v)] =
)v C (u) = [C (u)] = 0 and limv!v kt (v) = [1
t C (uv ) ; and condition (31) implies that limu!(1
0: Claim 2 can then be established by appling the mean value theorem to the left hand side of (50).
41
all
6=
1 ; m:
Since u
^ < uv (m1 ) ; w
^ > wv (m1 ) and
1 uv
(m1 ) + wv (m1 ) =
^v
1u
+ w
^v ; this
allocation is incentive compatible and delivers utility v to the agent. Then
n
h
E^v u
=
^
t C (u) + kt+1 (w)
( 1 ) ff (^
xv )
f (0)g +
i
o
W
(^
)
t
v
t
t fWt ( v )
n
E
Wt (^ v )g :
v
h
i
^ kt+1 (w)
C
(u)
+
t
u
t Wt (
The second term is …nite since Wt is bounded by Lemma 2, therefore this expression is positive
for high v from Claim 3. This contradicts the optimality of (uv ; wv ;
Using these arguments we can also rule out type
1
v) :
sending the same message as
2
with
any positive probability. Then the optimality condition (30) implies that
n
1 uv
(m1 )
o n
^
1 uv (m2 )
t C (uv (m1 )) + kt+1 (wv (m1 ))
o
^
t C (uv (m2 )) + kt+1 (wv (m2 ))
is bounded because the expression on the right hand side of (30) is bounded for all : Therefore
the value of this strategy can exceed the value of strategy when
1
and
2
send message m2
with probability 1 by only a …nite amount. But then the arguments of the previous paragraph
lead to a contradiction.
Part 2 of Corollary 2 is proven using analogous arguments. Here we consider function
F (x)
When
j j
uv mjMv j + x
j j 1
j j
that F 0 (0) = const (1
establish that F (^
xv )
allocation for type
type
j j:
j j 1
v)
tC
>
and %
uv mjMv j + x + ^ t+1 kt+1 wv mjMv j
j j 1
+
j j
j j 1
j j 2
j j 1
x :
holds, we can show
0 ensures the boundary conditions. Previous arguments
F (0) ! 1: Note that the perturbation we consider leaves the same
j j 1,
and gives an allocation uv mjMv j + x
^v ; wv mjMv j
j j 1
x
^v to
This is incentive compatible but gives a higher value than v: The contradiction then
follows from the fact that kt (v) is a decreasing function for high enough v:
Proof of Lemma 3. Part (i). If v0 = 0 then uv0 ;0 (m; z) = wv0 ;0 (m; z) = 0 for all (m; z).
Thus, if v0 = 0, then also vt = 0 for all t > 0. The optimal
t and, by Lemma 2,
t
thus minimizes Wt ( ) for all
is uninformative for all t. Suppose that the sustainability constraint
(10) binds in periods t = 0; :::; T + 1. By Theorem 1, for all t = 1; :::; T there exists vt > 0
such that if vt
vt
vt ;t (
jz; ) is uninformative and wvt ;t (m; z) is independent of z. By
Lemma 8, if v0 ! 0 then v1 = wv0 ;0 (m; z) ! 0 for all (m; z). In turn, the latter implies that
v2 = wv1 ;1 (m; z) ! 0. Proceeding recursively, we can therefore …nd v0 such that vt < vt for
t = 1; :::; T .
Part (ii). Suppose the assumptions of Theorem 1 are satis…ed (the other case is analogous.)
42
o
v)
Then there exists v0+ such that
v0 ;0
reveals full information about each type for all v0
v0+ .
Also, the FOCs imply
^
and, moreover, k00 (v) !
t+1
E
v0 ;0
k10 (wv0 ;0 ) jz = k00 (v)
1 as v ! v. The latter implies that there cannot be a constant
K < v such that wv0 ;0 (m; z)
K with probability 1, otherwise, the FOCs would be violated
for a high enough v0 . Thus, we can always …nd a high enough v0 such that wv0 ;0 (m; z) > v1+
with positive probability. Following analogous steps as in part (i), we can guarantee that
vt = wvt
1 ;t
1 (m; z)
> vt+ with positive probability for all t = 1; :::; T .
43
References
Acemoglu, Daron, “Why not a political Coase theorem? Social con‡ict, commitment, and
politics,” Journal of Comparative Economics, December 2003, 31 (4), 620–652.
, Mikhail Golosov, and Aleh Tsyvinski, “Political economy of mechanisms,” Econometrica, 2008, 76 (3), 619.
,
, and
, “Dynamic Mirrlees Taxation under Political Economy Constraints,” Review
of Economic Studies, 2010, 77 (3), 841–881.
Aiyagari, S. Rao and Fernando Alvarez, “E¢ cient Dynamic Monitoring of Unemployment
Insurance Claims,” Mimeo, University of Chicago, 1995.
Akerlof, George A., “The Economics of "Tagging" as Applied to the Optimal Income Tax,
Welfare Programs, and Manpower Planning,” The American Economic Review, 1978, 68
(1), pp. 8–19.
Albanesi, Stefania and Christopher Sleet, “Dynamic optimal taxation with private information,” Review of Economic Studies, 2006, 73 (1), 1–30.
Atkeson, Andrew and Robert E. Lucas, “On E¢ cient Distribution with Private Information,” Review of Economic Studies, 1992, 59 (3), 427–453.
and
, “E¢ ciency and Equality in a Simple Model of E¢ cient Unemployment Insurance,”
Journal of Economic Theory, June 1995, 66 (1), 64–88.
Benveniste, L M and J A Scheinkman, “On the Di¤erentiability of the Value Function
in Dynamic Models of Economics,” Econometrica, May 1979, 47 (3), 727–32.
Besley, Timothy and Stephen Coate, “Sources of Ine¢ ciency in a Representative Democracy: A Dynamic Analysis,” American Economic Review, March 1998, 88 (1), 139–56.
Bester, Helmut and Roland Strausz, “Imperfect Commitment and the Revelation Principle: the Multi-agent Case,” Economics Letters, November 2000, 69 (2), 165–171.
and
, “Contracting with Imperfect Commitment and the Revelation Principle: The Single
Agent Case,” Econometrica, July 2001, 69 (4), 1077–98.
and
, “Contracting with imperfect commitment and noisy communication,” Journal of
Economic Theory, September 2007, 136 (1), 236–259.
44
Bisin, A. and A.A. Rampini, “Markets as bene…cial constraints on the government,”Journal of Public Economics, 2006, 90 (4-5), 601–629.
Chari, V V and Patrick J Kehoe, “Sustainable Plans,” Journal of Political Economy,
August 1990, 98 (4), 783–802.
and
, “Sustainable Plans and Debt,” Journal of Economic Theory, December 1993, 61
(2), 230–261.
Clementi, Gina Luca and Hugo A Hopenhayn, “A Theory of Financing Constraints and
Firm Dynamics,” The Quarterly Journal of Economics, 02 2006, 121 (1), 229–265.
Dovis, Alessandro, “E¢ cient Sovereign Default,” Mimeo, Penn State, 2009.
Farhi, Emmanuel and Ivan Werning, “Inequality and Social Discounting,” Journal of
Political Economy, 2007, 115 (3), 365–402.
and
, “Insurance and Taxation over the Life Cycle,” Review of Economic Studies, 2013,
80 (2), 596–635.
, Christopher Sleet, Ivan Werning, and Sevin Yeltekin, “Non-linear Capital Taxation
Without Commitment,” Review of Economic Studies, 2012, 79 (4), 1469–1493.
Fernandes, Ana and Christopher Phelan, “A Recursive Formulation for Repeated Agency
with History Dependence,” Journal of Economic Theory, 2000, 91 (2), 223–247.
Freixas, Xavier, Roger Guesnerie, and Jean Tirole, “Planning under Incomplete Information and the Ratchet E¤ect,” Review of Economic Studies, April 1985, 52 (2), 173–91.
Golosov, Mikhail, Aleh Tsyvinski, and Iván Werning, “New dynamic public …nance:
A user’s guide,” NBER Macroeconomics Annual, 2006, 21, 317–363.
and
, “Designing optimal disability insurance: A case for asset testing,” Journal of
Political Economy, 2006, 114 (2), 257–279.
, Maxim Troshkin, and Aleh Tsyvinski, “Optimal Dynamic Taxes,” NBER working
paper 17642, 2011.
Green, E. J., “Lending and the Smoothing of Uninsurable Income,” in E. C. Prescott and
N. Wallace, eds., Contractual Arrangements for Intertemporal Trade, Minneapolis: University of Minnesota Press., 1987.
45
Hopenhayn, Hugo A and Juan Pablo Nicolini, “Optimal Unemployment Insurance,”
Journal of Political Economy, April 1997, 105 (2), 412–38.
Hosseini, Roozbeh, Larry E. Jones, and Ali Shourideh, “Optimal Contracting with
Dynastic Altruism: Family Size and per Capita Consumption,”Journal of Economic Theory,
2013, 148 (5), 1806–1840.
Kocherlakota, Narayana, The New Dynamic Public Finance, Princeton University Press,
USA, 2010.
Kydland, Finn E and Edward C Prescott, “Rules Rather Than Discretion: The Inconsistency of Optimal Plans,” Journal of Political Economy, University of Chicago Press, June
1977, 85 (3), 473–91.
La¤ont, Jean-Jacques and Jean Tirole, “The Dynamics of Incentive Contracts,” Econometrica, September 1988, 56 (5), 1153–75.
Ljunqvist, Lars and Thomas Sargent, Recursive Macroeconomic Theory, MIT Press, 2004.
Luenberger, David, Optimization by Vector Space Methods, Wiley-Interscience, 1969.
Marcet, Albert and Ramon Marimon, “Recursive Contracts,”Mimeo, European University Institute, 2009.
Milgrom, Paul and Ilya Segal, “Envelope Theorems for Arbitrary Choice Sets,” Econometrica, March 2002, 70 (2), 583–601.
Mirrlees, James, “An Exploration in the Theory of Optimum Income Taxation,” Review of
Economic Studies, 1971, 38 (2), 175–208.
Myerson, Roger B., “Optimal Coordination Mechanisms in Generalized Principal-Agent
Problems,” Journal of Mathematical Economics, June 1982, 10 (1), 67–81.
Phelan, Christopher, “Opportunity and Social Mobility,”Review of Economic Studies, 2006,
pp. 487–505.
and Robert M Townsend, “Computing Multi-period, Information-Constrained Optima,”
Review of Economic Studies, Wiley Blackwell, October 1991, 58 (5), 853–81.
Roberts, Kevin, “The Theoretical Limits of Redistribution,” Review of Economic Studies,
April 1984, 51 (2), 177–95.
46
Rockafellar, R.T., Convex Analysis Princeton mathematical series, Princeton University
Press, 1972.
Royden, H.L., Real Analysis Mathematics and statistics, Macmillan, 1988.
Rudin, Walter, Principles of Mathematical Analysis, third ed., New York: McGraw-Hill
Book Co., 1976.
Skreta, Vasiliki, “Sequentially Optimal Mechanisms,”Review of Economic Studies, 2006, 73
(4), 1085–1111.
Sleet, Christopher and Sevin Yeltekin, “Credibility and endogenous societal discounting,”
Review of Economic Dynamics, July 2006, 9 (3), 410–437.
and
, “Politically credible social insurance,” Journal of Monetary Economics, 2008, 55
(1), 129–151.
Stantcheva, Stefanie, “Optimal Taxation and Human Capital Policies over the Life Cycle,”
working paper, 2014.
Stokey, Nancy L., Robert E. Lucas, and Edward C. Prescott, Recursive Methods in
Economic Dynamics, Cambridge, MA: Harvard University Press, 1989.
Thomas, J. and T. Worrall, “Income Fluctuation and Asymmetric Information: An Example of a Repeated Principal-agent Problem,” Journal of Economic Theory, 1990, 51 (2),
367–390.
Yared, Pierre, “A dynamic theory of war and peace,”Journal of Economic Theory, September 2010, 145 (5), 1921–1950.
47
8
Supplementary material
8.1
Proofs for Section 3
Lemma 10 (a) Any PBE ( ;
is payo¤ -equivalent to a PBE ( 0 ;
G ; p)
0 ; p0 )
G
0
where
sat-
is…es
St
0
t
1
t
; Mt ; ht ; ~
(b) Suppose ( ;
^ t; h
~t 2 Ht
ries h
" 1
X
s
E( ; G )
G ; p)
t 1
1
;
St
0
t
=
t
1
t
; Mt ; ht ; ^
s us
S
t 1
^t
; Mt ; h
#
= E(
;
G)
"
1
X
0 ; p0 ) payo¤ equivalent
G
t+s
S
S t 1 ; Mt ; Mt+s
for all (zt+1 ; mt+1 ; :::; zt+s ) ; all
u0t+s S t+s
1
1
^ t ; zt+1 ; mt+1 ; :::; zt+s
; Mt+s ; h
t
: St !
t
t 1
0
t
S
Ht
B; d
t 1
t 1
St
t
; Mt ; B; ^
1 ; M ; B;
t
R
~
t 1
;^
;
t 1
~
B; d
for some ^
St
R
t
A ; ^
1
t 1
B
t 1
;
St
t
R
;
t
0
;~
1 ; M ; ht ;
t
; Mt ; h
#
:
(51)
with a property that
~ t ; zt+1 ; mt+1 ; :::; zt+s ;
; Mt+s ; h
~ t ; zt+1 ; mt+1 ; :::; zt+s ; mt+s :
; Mt+s ; h
analogously to the de…nition
t;
0
t
t
ht ; ^
1
;
t
t 1
;
t 1
ht ; d
t
St
0
t
= 0; set
t
t 1
B; d
t
;
;
jS t
t
1; M
t
t 1; M
t jS
t
^t
1 ; M ; B;
t
1
;
t
=
:
t 1
~
t 1
;
=
t
t 1
A ;
;
t
t
ht ; ~
St
0
t
1 ; M ; ht ;
t
> 0 only if
1
;
t
^t
1
;
t
t 1
A ; ^
for all
;
>0
t
can replicate the strategy of
t
and achieve the same payo¤ as that agent, and
t
is the optimal choice of agent ht ; ^
t
S
~t
by
1 ; M ; ht ;
t
t 1; M
t jS
t
t 1 t 1
: Since any agent with a history
the agent with a history
s us
t 1
1
1
; t:
and personal histo-
G ; p)
jS t+s
Ht
M !
for all ^
t
0
t
1
to ( ;
= u0t+s S t+s
> 0 de…ne strategy
: For any Borel set A of
t 1
t
=
t
;
: St
t 1
;^
in the text. Let B be a Borel set of H t : For all B such that
1; M
t
t
t 1
By construction,
t 1
jS t
t 1
For B such that
0
t
;
t
t
1
1; M
t
s t 1
0
t+s
=
^ t ; zt+1 ; mt+1 ; :::; zt+s ; mt+s
; Mt+s ; h
Proof. (part a). De…ne
of
R
t
for all ~
t
s=t+1
Then there exists a PBE ( 0 ;
jS t+s
;
is a PBE and suppose that for some S t
s=t+1
0
t+s
1
1
;
; the new strategy
t
0
satis-
…es agents’best response constraint (4).
Strategies
0
induce distribution
government strategy
G
0
which satis…es
0
t
=
satis…es feasibility (2) if agents play
i
t
for all S t
0:
1; M
t
; hence the
Any posterior belief p0 that
t
all ^
1
:
satis…es (3) also satis…es
payo¤ is
E(
0;
t ut jS
G)
t
R
=
t 1
Z
Ht
=
Z
Ht
and therefore ( 0 ;
0 ; p0 )
G
p0t
Z
Z
t 1
;
j d
t 1
=
R
p0t
jS t ; ht
d
ut ht
pt
jS t ; ht
d
ut ht d
t
j d
G ; p) :
is a PBE that is payo¤ equivalent to ( ;
0
G
by
00
00
(z) = z= and
: ( ; 1] ! [0; 1] by
o
n
^ t; h
~ t ; t+s as
for all s 1, ht 2 h
0
t+s
if zt+1
jht ; zt+1 ; mt+1 ; :::; zt+s ;
t+s
(z) = (z
=
t+s
t ut jS
G)
0
G
t
;
gives a
0
G
when agents play
: Therefore
G ; p) :
0
and assume that
0
: [0; ] ! [0; 1]
) : De…ne strategies ( 0 ;
) = (1
~ t;
= ut+s h
u0t+s ht ; zt+1 ; mt+1 ; :::; mt+s
;
because otherwise
(part b). For simplicity we drop explicit dependence on S t ; Mt+1
~t ;
^ t > 0: Let
~t =
~t +
^t
= t h
and de…ne
h
t h
t h
t h
0
: Government’s
No strategy
when agents play
G
t 1
dht jS t = E(
t
would give a higher payo¤ to the government that strategy
0 ; p0 )
G
;
dht jS t
0
t
achieves the same payo¤ as ( ;
higher payo¤ to the government that strategy
( 0;
t 1
pt
t 1
0 )
G
(zt+1 ) ; mt+1 ; :::; mt+s ;
~ t;
jh
0
(zt+1 ) ; mt+1 ; :::; zt+s ;
t+s
and
^ t;
= ut+s h
u0t+s ht ; zt+1 ; mt+1 ; :::; mt+s
0
t+s
if zt+1 >
jht ; zt+1 ; mt+1 ; :::; zt+s ;
and u0s = us ;
t+s
=
t+s
00
^ t;
jh
(zt+1 ) ; mt+1 ; :::; mt+s ;
00
(zt+1 ) ; mt+1 ; :::; zt+s ;
t+s
0
s
= us for all other histories and periods s:
~ t; h
^ t could have replicated each other strategies after period t in
Agents with histories h
so they must have been indi¤erent between them. Pro…le 0 gives them the
n
o
^ t; h
~ t leaving all other histories unchanged, therefore
same utility for all histories following h
PBE ( ;
G ; p),
it is incentive compatible, i.e. satis…es (4). Strategy pro…le
probability for any realization of ut as
any p0 consistent with Bayes’rule, E
Therefore ( 0 ;
8.2
0 ; p0 )
G
0
It assigns the same
; therefore feasibility constraint (2) is satis…ed. For
t jh
t
=E
0
t jh
t
for all ht 2 H t hence (5) is satis…ed.
is a PBE which is payo¤ equivalent to ( ;
G ; p) :
Arguments for maximization problem (17) and recursive formulation
We …rst discuss convexity assumptions in problem (17). We have
ut :
0:
induces
Ht
! [(1
) v; (1
) v] : Let
t
t
: Ht
!
be a space of all such ( t ; ut ), and let
ii
(Mt ) ;
t
be a
probability measure on t : For any t and random variable x : t
! R we can deR
…ne E t x =
x (ut (m) ; t ; ) t (dmj ) d d and for an arbitrary 0t let E t 0t x =
t Mt
R
x (ut (m) ; t ; ) 0t (dmj ) d d : As before let to denote the in…nite sequence f t g1
t=0
t Mt
and extend the de…nition of expectation E
1
to V
M1
1:
With this notation,
the modi…ed problem (9) can be written as
1
X
max E
t
u
t=0
subject to
E C (u)
E
1
X
s t
u
E Wt +
s=t
E
1
X
t
u
E
(52)
U (e) for all t;
1
1
X
0
t=0
and
e
t
(53)
0
u for all
(54)
t=0
E
"
1
X
t
u v
t=0
#
v:
(55)
Note that we wrote the promise keeping constraint (55) as inequality. We do this more general
version to prove some technical results on properties of the Lagrange multipliers. We still
maintain the assumption that distribution
is such that in the optimum it holds with equality.
The objective function and constraints are linear in
and
t
t
t
and therefore convex. Let
t
t
t
be the Lagrange multipliers on (52) and (53). Then the constrained maximization
problem can be written as
max E
1
X
t
t=0
"
1+
t
X
s=0
s
!
subject to (54), (55). Rede…ning variables
Pt
Pt
t= 1 +
s=0 s and t = t = 1 +
s=0
u
t
t C (u)
=
t
#
1+
E
1
X
t
t Wt
(56)
t=0
Pt
s=0
s
; ^t =
t= t 1;
t
=
0 we obtain (17) in a more general form.
> 0 implies ^ t > and t > 0: If lim supt!1 t >
s
From the de…nitions of these variables, t
P
0 then ts=0 s ! 1 (Theorem 3.23 in Rudin (1976)) and t = t ! 1. The arguments of
P
P1 t
P1 t
Sleet and Yeltekin (2008) establish that 1
t and
t are all …nite, and
t=0 t ;
t=0
t=0
P1
P1
therefore t=0 t t and t=0 t t are also …nite.
The Lagrange multiplier
t
> 0 in any …nite t: If it is not the case, then it is possible to give
lifetime utility v to all families, which violates feasibility. The technical arguments simplify if,
in addition, lim inf
t
> 0: Su¢ cient conditions for this result are given in the following lemma
iii
Lemma 11 Let
be the best PBE. Suppose either that
ution or that U is unbounded above and
lim inf u!1 CC(u)
0 (u)
t
converges to an invariant distrib-
> 0: Then lim inf
> 0:
t
Proof. We …rst observe that it is incentive compatible to increase utility allocation for all
histories by
> 0 and that this increase satis…es (55). First, suppose that U is unbounded
above. For
> 0 de…ne
and perturbation (1
)
1+
t
+
t
(56) evaluated at t ; i.e.
"Z "
From the de…nition of
by
t
t
X
s=0
( t ; ut + ) =
t
s
t
( t ; ut ) for all ( t ; ut ) : Since
t
is optimal
is feasible, this perturbation cannot increase the value of
!
u
t C (u)
#
#
h
t
t
C (u)] d
t
0:
(dmj ) d
d
i
0
t;
1+
t
X
s=0
s
!
t
Z
[C (u + )
Since it should be true for all ; it implies that
1
E t C 0 (u)
Suppose lim inf u!1
all u
e
C(u)
C 0 (u)
:
t
> 0; which implies that there is u
~ and
> 0 such that
C(u)
C 0 (u)
for
u
~: Feasibility implies
E t C (u) = E
E
t
t
[C (u) ju < u
~] P
C (u) 0
C (u) ju
C 0 (u)
u
~ P
t
t
(u
(u < u
~) + E
u
~)
E
t
t
C (u) 0
C (u) ju
C 0 (u)
C 0 (u) ju
u
~ P
t
u
~ P
(u
t
(u
u
~)
u
~) :
Therefore,
E t C 0 (u) = E
t
C 0 (u) ju < u
~ P
max C 0 (u) P
u2[0;~
u]
max C 0 (u) +
t
t
(u < u
~) + E
(u < u
~) +
t
e
C 0 (u) ju
u
~ P
t
(u
u
~)
e
u2[0;~
u]
From strict convexity of C, C 0 (~
u) = maxu2[0;~u] C 0 (u), therefore,
t
C 0 (~
u) +
e
1
> 0:
This proves the second part of the lemma. Analogous arguments establish our result for
invariant distribution since in the invariant distribution E C 0 (u) must be …nite.
iv
If assumption lim sup
> 0 is not satis…ed, economy converges to that of Atkeson and
t
Lucas (1992), who showed that for a wide range of cost functions C (including those satisfying
conditions of Lemma 11) all the mass of the lifetime utilities eventually gets concentrated
arbitrarily close to the lower bound v; the result known as the immiseration. Immiseration
violates constraint (16) and therefore lim sup
> 0 in all speci…cations considered by Atkeson
t
and Lucas (1992).
8.2.1
Sketch of proofs of Propositions 1 and 2
We now adapt the arguments of Farhi and Werning (2007) to write problem (17) recursively.
When
t
is strictly positive with lim inf
t
> 0; the series f t gt are bounded away from zero
uniformly in t. The arguments of Lemma A2 of Farhi and Werning (2007) extend with minimal
modi…cations to problem (17) to show that it can be written in a recursive form
kt (v) = max E
2
t
h
^
t C (u) + t+1 kt+1 (w)
u
t Wt
i
subject to
v = E [ u + w]
E [ u + w]
E
0
[ u + w] for all
0
;
where kt (v) is convex. To achieve convexity of this problem, it is su¢ cient to randomize
between only two points in
t
(the arguments are identical to the proof of Lemma 3 in Acemoglu
et al. (2008)), and hence this problem can be written as
Z
i
h
0
0
0
^
kt (v) =
max
z
u
t C u + t+1 kt+1 w
0
0 0
(u ;w ; );
(u00 ;w00 ; 00 );
z2[0;1]
+ (1
z)
(dmj ) d ( )
t Wt
0
00
(dmj ) d ( )
t Wt
00
Mt
Z
h
Mt
subject to
Z
v=z
0
0
u + w
0
0
u00
tC
u00 + ^ t+1 kt+1 w00
(dmj ) d ( ) + (1
Mt
z)
Z
i
u00 + w00
00
(dmj ) d ( )
Mt
and
Z
Z
u0 + w0
0
(dmj ) d ( )
Mt
Mt
u00 + w00
00
(dmj ) d ( )
Z
ZMt
Mt
v
u0 + w0 ~ (dmj ) d ( ) for all ~
u00 + w00 ~ (dmj ) d ( ) for all ~
This is the Bellman equation (20). Then Proposition 1 and 2 can be established by direct
adaptation of arguments in Farhi and Werning (2007). We show all the results for k0 ; for
all other kt the arguments are identical. For brevity we drop explicit conditioning of all
expectations on v:
Continuity
Since k0 (v) is concave, it is continuous on (v; v) : To show that it is also continuous on the
boundaries, de…ne the value function
k0 (v) =
1
max E
;u
0
1
X
t [ t ut
tC
1
X
(ut )] + max
t=0
subject to
t t Wt
t=0
1
X
v=E
t
!
t ut :
t=0
We have k0 (v)
k0 (v) and k0 (v) is continuous. If utility is bounded below, then at v = v;
the solution to k0 sets ut = U (0) for all t and
to minimize Wt : This allocation is incentive
compatible, therefore, k0 (v) = k0 (v) : Then continuity of k0 (v) at v implies continuity of k0 (v)
at v: If utility is bounded above, then C (ut ) ! +1 as v ! v: Therefore limv!v k0 (v) =
which implies limv!v k0 (v) =
1:
Di¤ erentiability
1,
The proof is an application of the Benveniste and Scheinkman theorem (Benveniste and
Scheinkman (1979)). First, suppose that utility is unbounded. Fix any interior v0 and let
(u ;
) be the optimal allocation for that v: For any v; let u
~0 = u0 + (v
v0 ) ; u
~t = ut for all
t > 0. Since utility is unbounded, this perturbation is feasible. Then (~
u;
) satis…es (11) and
(12) for v: Let
V (v) =
1
E
0
[
1
0
We have k0 (v)
~t
t [ tu
tC
(~
ut )
t Wt ]
0C
(u0 + (v
(57)
t=0
= E
+
1
X
0 (u0 +
1
X
E
(v
v0 ))
t [ t ut
tC
(ut )
v0 ))
0 W0 ]
t Wt ]
t=1
V (v) : Function V is di¤erentiable with V 0 (v0 ) = 1
0E
C 0 (u0 ) : Since
k0 is concave, by Benveniste-Scheinkman theorem (see Theorem 4.10 in Stokey et al. (1989)),
k00 (v) exists and satis…es k00 (v) = 1
0E
C 0 (u0 )
1:
To …nd the values of k00 (v) in the limit as v approaches
K (v) = max E
u;
1
X
t=0
vi
t
[ t ut
tC
1, de…ne a function
(ut )]
subject to (12).
It it easy to show that K (v) is concave and limv!
limv!1 K 0 (v) =
1:
Let
t
= max
2 ;c 0 [
U (c)
1
1 X
k0 (v)
t c]
t t
1
=
0 t=0
E
1
X
t
and ! t =
1
X
E
0
[ t ut
t C (ut )
t]
0 (v)
= 1 and
Wt ( ) : Then
t [ t ut
t C (ut )
t]
1
X
E
t=0
t=0
K (v)
t min
1K
t t Wt
t=0
1
X
t!t
t=0
1
X
t
t
t=0
1
X
t!t;
t=0
where the …rst inequality follows from the fact that the expression in square brackets is negative and t = 0
P1 t
[ t ut
E
t=0
Since k0 (v)
t
and the second inequality follows from the fact that K (v) maximizes
tC
(ut )] without incentive constraints.
K (v)+const and K (v) is concave, limv!1 K 0 (v) =
1: Since k00 (v)
1 and limv!
1K
0 (v)
= 1; limv!
0
1 k0 (v)
= 1:
1 implies limv!1 k00 (v) =
Now suppose that utility is bounded below but unbounded above. Without loss of general-
ity, assume that U (c)
v
v0 u
0. Then for any v0 ; the allocation
is feasible), incentive compatible and attains v: Let V (v) =
1
0
E
;
is feasible (since vv0 ut > 0
h
P1
v
v
t v0 ut
t C v0 ut
t=0 t
V (v) is concave, di¤erentiable and satis…es k0 (v0 ) = V (v0 ) ; therefore, k0 (v) is di¤erentiable at
v0 by the Benveniste-Scheinkman theorem. A symmetric argument works if utility is bounded
above (without loss of generality by 0) but not below. If utility is bounded above and below,
a function V can be constructed separately for v
v0 and v > v0 : This shows that k0 (v) is
di¤erentiable.
To establish the value of the derivatives in the limits, note that when utility is bounded,
function K (v) still provides an upper bound to k0 (v) and limv!v K 0 (v) =
that limv!v k00 (v) =
v
1; which implies
1: When utility is unbounded below, we can de…ne V as in (57) for
v0 , which shows that k00 (v0 )
0
0 E C (u0 )
limv! 1 k00 (v) = 1:
limv"v0 V (v0 ) = 1
arguments as for unbounded utility establish that
1: Then the same
It remains to show the value of limv!v k00 (v) when utility is bounded below, without loss
of generality by 0. Let
1
K (v) =
subject to (12). Let
max
1
X
t
0 ut 2R+ t=0
v
"
X
( )
2
!
ut
#
t C (ut )
1
1 X
t!t
0 t=0
be a Lagrange multiplier on (12) for a given v: The …rst order condition
for ut is
1
0
t C (ut )
vii
t
t= 0
v;
(58)
t Wt
i
:
where the inequality sign is due to the non-negativity constraint on ut : This expression implies
that
then
1: Therefore for the utilities bounded below, limv!v k00 (v)
v
t
t= 0
! 0 and there is some T such that 1
T
T= 0
v
1: If lim sup
t
> 0,
> 0: For such T the optimality
condition (58) is satis…ed only for uv;T > 0: This is impossible since limv!v uv;t = 0 for all t;
therefore if lim sup
t
> 0, then limv!v
v
= 1: From the envelope theorem, K 0 (v) =
K (v) and k0 (v) =
Since the solution to this problem is incentive compatible, k0 (v)
K (v) : Therefore
limv!v k00 (v)
0
limv!v K (v)
1 with
limv!v k00 (v)
v:
= 1 if lim sup
t
> 0:
The arguments for the proof of Proposition 2 mirror the proof of Theorem 2 in Farhi and
Werning (2007).
8.3
Intermediate steps used in the proof of Theorem 2 and Corollary 2
We start with preliminary results.
Lemma 12 Suppose that f is continuous on some interval [a; b] and one of its Dini derivatives
is bounded. Then f is Lipschitz continuous on [a; b] :
Proof. Without loss of generality suppose that D+ f (t) ; de…ned as
D+ f (t)
lim sup
h!0+
is bounded by D: Let
1 (t)
f (t + h)
h
f (t)
;
= f (t) + Dt: It is continuous since f is continuous and D+
D+ f (t)+D
0: By Proposition 5.2 in Royden (1988)
implies f (t00 )
f (t0 )
D (t00
1
=
is nondecreasing, and therefore t00 > t0
t0 ) : Applying the same arguments to
combining with the previous result, we establish jf (t00 )
1 (t)
f (t0 )j
2 (t)
D jt00
=
f (t) + Dt and
t0 j for all t00 ; t0 2 [a; b] :
Lemma 13 If Assumption 1 is satis…ed, then
lim
u!(1
In particular, for any v (1
C 0 (^
u)
)v
C 00 (u)
= 0:
[C 0 (u)]2
) < a < b < v (1
C 0 (~
u)
Ba;b j^
u
(59)
) there exists a real number Ba;b such that
u
~j for all u
^; u
~ 2 [a; b] :
Moreover, for any " > 0; there is a such that Ba;b = (C 0 (b))2 < " for all b > a
(60)
a:
For any v < a < b < v such that kt0 (a) < 1; function kt0 is Lipschitz continuous on [a; b]
^a;b such that
and there exist a real number B
v)
kt0 (^
kt0 (~
v)
^a;b j^
B
v
v~j for all v^; v~ 2 [a; b] :
^a;b = (1
Moreover, for any " > 0; there is a such that B
viii
kt0 (b))2 < " for all b > a
a:
Proof. By de…nition C (U (c)) = c for all c: Di¤erentiate twice
C 0 (U (c)) U 0 (c) = 1
and
C 00 (U (c)) U 0 (c)
2
+ C 0 (U (c)) U 00 (c) = 0:
(61)
Substitute the …rst expression into the second and regroup
U 00 (c)
:
U 0 (c)
C 00 (U (c))
=
[C 0 (U (c))]2
If Assumption 1 is satis…ed, we obtain (59). Since U 00 is continuous, so is C 00 from (61).
For any u
^; u
~ 2 [a; b] with u
~<u
^;
0
C (^
u)
0
C (~
u) =
Z
u
^
C 00 (u) du
(^
u
u
~) max C 00 (u) ;
u2[a;b]
u
~
where maximum is well de…ned since C 00 is continuous. Let u
^a;b = arg maxu2[a;b] C 00 (u) and
Ba;b = C 00 (^
ua;b ) : Since C 00 (^
ua;b ) = [C 0 (^
ua;b )]2
a ! (1
C 00 (^
ua;b ) = [C 0 (b)]2 and u
^a;b ! (1
) v; condition (59) establishes (60).
) v as
Since function kt is concave and di¤erentiable, kt0 is continuous on [a; b] (Corollary 25.5.1
in Rockafellar (1972)). Let D+ be the right upper Dini derivative of kt0 , de…ned at each v0 as
D+ kt0 (v0 )
lim sup
v!v0+
kt0 (v)
v
kt0 (v0 )
:
v0
Claim 1. D+ kt0 (v0 ) satis…es
0
D+ kt0 (v0 )
V 00 (v0 );
where V (v) is de…ned in (57).
Note that by construction V is twice di¤erentiable with V 00 (v0 ) =
tE
v0
[C 00 (uv0 )],
V (v)
kt (v) for all v with equality for v = v0 and V 0 (v0 ) = kt0 (v0 ) : Since kt0 is decreas-
ing, 0
D+ kt0 (v0 ) by de…nition. Suppose D+ kt0 (v0 ) < V 00 (v0 ): Then there exists v^ > v0 ; such
that for all v 2 (v0 ; v^) ; kt0 (v) < V 0 (v) : If this is not the case, there must exist a sequence vn ;
with vn ! v0+ ; such that kt0 (vn )
kt0 (vn )
vn
V 0 (vn ) or
kt0 (v0 )
v0
V 0 (vn )
vn
V 0 (v0 )
for all vn :
v0
Taking limits and invoking twice di¤erentiability of V;
D+ kt0 (v0 )
kt0 (vn )
vn
n!1
lim sup
ix
kt0 (v0 )
v0
V 00 (v0 ) ;
which contradicts the assumption.
If kt0 (v) < V 0 (v) for all v 2 (v0 ; v^) ; then
Z
Z v^
0
kt (v) dv <
v^
V 0 (v) dv;
v0
v0
where the integrals are well de…ned since kt and V are concave and hence absolutely continuous
by Proposition 5.17 in Royden (1988). Integrating and using the fact that kt (v0 ) = V (v0 ) ; we
obtain kt (^
v ) < V (^
v ) ; establishing the contradiction. Therefore D+ kt0 (v0 )
V 00 (v0 ):
Claim 2. kt0 is Lipschitz continuous on [a; b].
It is su¢ cient to show that V 00 (v0 ) =
tE
v0
[C 00 (uv0 )] is bounded on [a; b] and apply
Lemma 12. From (28),
kt0 (a)
1
tC
1
0
(uv0 )
1
kt0 (b)
j j
for all v0 2 [a; b] :
(62)
Since kt0 (a) < 1; this bounds uv0 : C 00 achieves a maximum at that set, say at a point u
^a;b ,
^a;b = t C 00 (^
ua;b ) :
which implies that V 00 (v0 ) is bounded by B
^a;b satis…es the condition that for any " > 0; there is a such
Claim 3. Lipschitz bound B
2
^a;b = (1 kt0 (b)) < " for all b > a a:
that B
As a ! v; kt0 (a) !
close to (1
1 and therefore equation (62) implies that u
^a;b gets arbitrarily
) v for all a su¢ ciently high. By the …rst part of the lemma, this implies that
C 00 (^
ua;b ) = [C 0 (^
ua;b )]2
approaches zero for high a: Hence
^a;b
B
[1
kt0 (b)]2
=
00 u )
a;b
t C (^
[C 0 (^
ua;b )]2
C 0 (^
ua;b )
1 kt0 (b)
2
00 u )
a;b
t C (^
[C 0 (^
ua;b )]2
j j
2
t
also approaches 0 as a ! v:
8.4
Proof of Proposition 4
Suppose C satis…es
C (u) =
1 a
u for a > 1:
a
(63)
For all x > 0; de…ne a function
kt (v; x) =
1
max E
t u;
"
1
X
s us x
s+t
a 1
s+t C
(us )
xa
s=0
subject to (11) and (12). For x = 0 we set
kt (v; 0) =
1
max E
t u;
"
1
X
s=0
We prove several preliminary result …rst.
x
s+t
s+t C
(us )
#
:
s+t Ws
#
Lemma 14 Suppose C satis…es (63). Then kt (v; x) is continuous in (v; x) :
Proof. For interior (v; x) it is immediate, so we show our result for boundary: if (vn ; xn ) !
(v; 0) then kt (vn ; xn ) ! kt (v; 0) : Since jkt (vn ; xn )
jkt (v; xn )
kt (v; 0) j
kt (v; 0) j; and kt (v; x) is continuous in v for all x
jkt (vn ; xn )
kt (v; xn ) j +
0 by standard arguments, it is
su¢ cient to establish that kt (v; xn ) ! kt (v; 0) as xn ! 0:
We show our result for k0 (v; x) ; the arguments are analogous for other periods. Let
1
X
K (v; x) = max E
u;
t
xa
1
t ut
tC
(ut )
t=0
subject to (12). Analogously with the proof of Proposition 1, K (v; x) is …nite for all x
k0 (v; x)
K
(v; x) + xa
0 and
const, therefore k0 (v; x) is bounded from above, and that bound can
be chosen to be uniform for all x in the neighborhood of x = 0. Function k0 (v; x) is bounded
below because u
0; C (u)
0 and Wt is bounded. Moreover, that bound can be chosen to
be uniform for all x in the neighborhood of x = 0.
Let (ux ;
x)
be a solution to k0 (v; x) for a given x: We show next that
for all x in the neighborhood of x = 0: Since
such that
and
b00
tC
(u)
b0t
00
j j bt u
(u) is convex, there are
for all u: Since
t
x
t ut is bounded
reals b0t and b00t > 0
zero, we can pick b0
t=0
is bounded away from
to be independent of t: Then
0 k0 (v; x) = E
b0
b0
x
1
X
t
xa 1
<
0
t=0
1
X
this yields
E
x
t
uxt
t=0
Since (ux ;
x)
1
x
t C (ut )
uxt
xa E
x
1
X
t t Wt
t=0
t+E
b00
1
X
xa
t=0
1
X
t+E
t=0
For
tC
P1
x
x
1
X
t=0
1
X
t
t
xa
xa
1
1
uxt
j
00 x
j b ut
uxt
b00
xa E
xa E
b00
1
1
X
t t Wt
t=0
x
1
X
t t Wt :
t=0
t=0
b0
xa
x
1
X
t
xa E
x
t=0
1
X
t t Wt
0 k0 (v; x) :
t=0
are optimal for x; incentive compatible and provide utility v to agent,
"1
#
"1
#
X
X
0
x
E 0
E x
t
t C ut
t(
t C (ut )) ;
t=0
t=0
P
x
where the right hand side expression is well de…ned since k0 (v; x) and E x 1
t=0 t ut are
P1
x
…nite, which implies that k0 (v; 0) lim supx!0 E x
t C (ut )) : At the same time
t=0 t (
"1
#
"1
#
X
X
x a 1
x
0 a 1
0
E 0
k (v; x) = E x
xa t Wt
xa t Wt
t ut x
t ut x
t
t C (ut )
t
t C ut
t=0
t=0
xi
which implies that
lim inf k0 (v; x) = lim inf E
x!0
x
x!0
where again we used boundedness of E
x
all v:
"
P1
1
X
t(
tC
t=0
t
t=0
#
(uxt ))
k (v; 0) ;
uxt : Therefore limx!0 k0 (v; x) = k0 (v; 0) for
First, we analyze the limiting case of x = 0: It has a recursive structure
h
kt (v; 0) = max E
u;w;
i
^ kt+1 (w; 0)
C
(u;
0)
+
t
t+1
subject to (22) and (21). Any conditioning on z is redundant since C ( ; u) is strictly convex
and then the Revelation principle implies strict convexity of kt ( ; 0). One can also easily show
that kt ( ; 0) is di¤erentiable and decreasing.
Let u0v (m) ; wv0 (m) ;
0
v
(mj )
;m
be a solution to this problem.
Lemma 15 Suppose that u0v (m0 ) ; wv0 (m0 ) 6= u0v (m00 ) ; wv0 (m00 ) for some m0 ; m00 ;
0
v
0 and
(m0 j ) >
u0v m0 + wv0 m0 = u0v m00 + wv0 m00 :
Then
tC
and
0
v
u0v m0
+ ^ t+1 kt+1 wv0 m0
>
tC
u0v m00
+ ^ t+1 kt+1 wv0 m00
(64)
(m00 j ) = 0:
Proof. Suppose
tC
u0v m0
+ ^ t+1 kt+1 wv0 m0
Then setting ~ 0v (m00 j ) =
0
v
(m00 j ) +
<
0
v
tC
u0v m00
+ ^ t+1 kt+1 wv0 m00
:
(m0 j ) ; ~ 0v (m0 j ) = 0 and leaving all other re-
porting strategies unchanged satis…es (22) and (21) and delivers a strictly higher value of
h
i
^ kt+1 (w; 0) ; contradicting optimality of 0 (m0 j ) > 0:
E
C
(u)
+
t
t+1
v
Suppose (64) holds with equality. De…ned as u
~ =
wv0 (m0 ) + (1
) wv0 (m00 ) for some
u0v
(m0 ) ; wv0 (m0 )
u0v (m0 ) + (1
) u0v (m00 ) and w
~ =
2 (0; 1) : The new allocation satis…es (21) since
u0v
(m00 ) ; wv0 (m00 )
indi¤erent between
and
any ^ 6= and m
^ that ^ sends with a positive probability,
0
^u0 (m)
^
v ^ + wv (m)
: It also satis…es (22) since for
^u0 m0 + w0 m0
v
v
xii
is
and
0
^u0 (m)
^
v ^ + wv (m)
^u0 m00 + w0 m00
v
v
and therefore
0
^u0 (m)
^
v ^ + wv (m)
For any , by strict concavity of
tC
^u
~ + w
~ :
C and kt+1
(u ) + ^ t+1 kt+1 (w ) >
tC
u0v m0
+ ^ t+1 kt+1 wv0 m0
=
tC
u0v m00
+ ^ t+1 kt+1 wv0 m00
(65)
:
Augment the message space Mv with a message m? : De…ne ~ (m? j ) = 0v (m0 j ) +
0 (m00 j ) and ~ m j^ = 0 for all ^ =
6
; and ~ (mj ) = 0v (mj ) for m 2
= fm0 ; m00 ; m? g,
?
v
~ mj^ =
0
v
mj^ for all ^ 6=
and all m 6= m? : Similarly let (~
u (m? ) ; w
~ (m? )) = (u ; w )
2 (0; 1) and (~
u (m) ; w
~ (m)) = u0v (m) ; wv0 (m) for all m 6= m? : That is we consider
for any
an augmented state space and a strategy in which type
reports m? and receives (u ; w ) in
all states in which she reported m0 ; m00 leaving all other strategies and allocations unchanged.
The 3-tuple (~
u; w;
~ ~ ) is incentive compatible and delivers the same payo¤ v to the agent, but
by (65) and the fact that ~ (m? j ) > 0 delivers strictly higher value to the planner. Therefore
0
v
u0v ; wv0 ;
cannot be optimal, leading to a contradiction.
This lemma shows that each type can receive only one distinct allocation. Under some
additional conditions requiring types to be su¢ ciently spread out, we can also show that each
receives a distinct allocation from other types.
Lemma 16 Suppose condition (33) is satis…ed. Then if
0
v
0
mi j
= 0 for all
0
6= :
0
v
(mi j ) > 0 for some
; then
Proof. Previous lemma established that types can receive at most j j distinct allocations,
so we restrict attention to only j j messages. Without loss of generality u0v (m1 )
u0v
mj
j
: Suppose that there is an allocation
u0v
(mn ) ; wv0 (mn )
:::
that two types receive with
a positive probability. Due to the previous lemma, they must receive it with probability 1.
Pick the highest type that receives an allocation which is also received by some lower type.
To simplify notation, call that type
receives
u0v (mn
u0v
(mn 1 ) ; wv0 (mn 1 )
=
n
and the single crossing property implies that
u0v
(mn ) ; wv0 (mn )
. For now assume that
1) :
First, observe that it must be true that
0
n+1 uv
(mn+1 ) + wv0 (mn+1 ) >
xiii
0
n+1 uv
(mn ) + wv0 (mn ) :
u0v
n 1
(mn
also
2)
<
Otherwise, if this inequality is weak, the fact that u0v (mn+1 ) ; wv0 (mn+1 ) 6= u0v (mn ) ; wv0 (mn )
implies
0
n uv
(mn ) + wv0 (mn ) >
0
n uv
(mn+1 ) + wv0 (mn+1 ) :
But then wv0 (mn+1 ) can be decreased and wv0 (mn ) increased while keeping
0
n+1 ) wv (mn+1 )
(
(
0
n ) wv (mn )
+
constant. For small changes that will be incentive compatible, and strict
concavity of kt+1 ( ; 0) will imply that the perturbed allocation gives a higher value, contradicting optimality.
Choose " > 0 small enough so that
0
n+1 uv
Let
2 (")
=
(mn+1 ) + wv0 (mn+1 ) >
n 1
";
3 (")
1 (") =
1
=
(
n 1
n
n 2
1) [
0
n+1 uv
(mn ) + wv0 (mn ) +
(
n+1
(
n)
n 1)
":
" and
n
n
1] " +
n 1
n 2
n
X2
( i ) ":
i=1
By construction, all
1 (")
are positive and O (") ; and
8
1<
( n 1) [ n
(
3 (") =
n 1]
:
n 2)
n 1
j j
X
i=n 1
if condition (33) is satis…ed.
Consider an allocation (~
u; w)
~ de…ned as
u
~ (mn ) = u0v (mn ) +
u
~ (mn
1)
= u0v (mn
1)
(
(
";
n 1)
n)
u
~ (mi ) = u0v (mi ) for i 2
= fn
";
1; ng ;
and
w
~ ( i ) = wv0 ( i ) +
3 (")
w
~ ( i ) = wv0 ( i )
1 (")
1 (")
for i
for i > n;
n 1)
w
~ ( n ) = wv0 ( n )
2 (")
( n)
w
~ ( n 1 ) = wv0 ( n 1 ) + 2 (")
1 (") :
(
xiv
n
1 (") ;
2;
9
=
( i) "
;
0
First, observe that (~
u; w)
~ satisfy (21) since
j j
X
j j
X
( i) [ iu
~ (mi ) + w
~ (mi )]
i=1
=
(
n 1) ( n
n 1) "
+
3 (")
0
i uv
( i)
i=1
n
X2
( i)
(mi ) + wv0 (mi )
1 (")
i=1
=
(
n 1) ( n
n 1) "
+(
n 1
n 2) "
n
X2
( i)
(
n 1) [ n
n 1] "
+(
n 2)
n 1
i=1
= 0:
j
( i) "
i=1
It also satis…es incentive compatibility. Note that for small " we have u
~ (m1 )
u
~ mj
n
X2
:::
and it su¢ ces to check local downward incentive compatibility. We have
~ (mn 1 )
n 1u
=
n 1
+ w
~ (mn 1 )
n
( n 1)
"+ 1+
1+
( n)
so the incentive constraint for type
~ (mn 2 )
n 2u
=
n 2"
so the incentive for type
+(
n 2
n 1
n 1
~ (mn )
1u
(
w
~ (mn )
n 1)
(
2 (")
n)
= 0;
is satis…ed. Also
+ w
~ (mn
2)
n 2) "
~ (mn 1 )
n 2u
n 1"
w
~ (mn
1)
= 0;
is satis…ed. Similar arguments hold for all the other incentive
constraints. Finally
j j
X
( i)
i=0
=
n
X2
h
i
^
C
(~
u
(m
))
+
k
(
w
~
(m
))
i
i
t
t+1 t+1
0
( i ) kt+1
(w
~ (mi )) (
3 (")
1 ("))
X
( i)
h
0
0
^
t C uv (mi ) + t+1 kt+1 wv (mi )
0
( i ) kt+1
(w
~ (mi )) (
1 ("))
+ o (") :
i=n+1
0
Since kt+1
< 0 and under condition (33) (
3 (")
positive for " small enough. This shows that
If u0v (mn
i=0
j j
+
i=0
j j
X
2)
= u0v (mn
1) ;
1 ("))
u0v ; wv0
0; the expression above is strictly
cannot be optimal.
then the same steps as before go through if u0v (mi ) is reduced
by " for all i such that u0v (mi ) = u0v (mn
1)
and
are adjusted accordingly.
We are now ready to prove Proposition 4.
Proof of Proposition 4.
The solution to Bellman equation (20) may involve random-
ization over several v~v (z) that in expectations deliver v; but v~v (z) ! 1 for all z as v ! 1.
Consider maximization problem for a given z and assume that agents send reports over the
message set M
for all v: Using homogeneity properties of kt (v) ; if (u0v ; w0 ;
xv
v)
is a solution
i
!
to kt (v), then (ux ; wx ;
x=v
x)
1
max E
u;w;
subject to (22) and
v
h
xa
1
1
u0v ; v
1
wv0 ;
v
is a solution to the following problem for
^
t C (u) + t+1 kt+1 (w; x)
u
i
xa t Wt ( )
1 = E [ u + w] :
Since u; w are bounded from below by 0, arguments analogous to (45) establish that
h
i
2 0; ( ( 1 ) ) 1 and that ux (m) lies in a compact set. Since Lemma 14 estab-
wx (m)
lished that kt+1 (w; x) is continuous in x; the Theorem of Maximum applies and solution
correspondence (ux ; wx ;
x)
is u.h.c. in x:
We show that there cannot be several types
that send the same message m with a positive
probability for low x; which establishes the result of the Proposition. First, observe that there
must be some threshold x; such that for all x
x no two types send the same message with
probability 1. If this is not the case, we can choose a sequence xn ! 0 with solution
xn
satisfying such property, which by u.h.c. of
0
would imply that
xn
satis…es this property,
violating Lemma 16.
Next we rule out that several types send the same message with positive probability. Suppose that for any x we can …nd some x < x with this properties. There must be some type
who is indi¤erent between messages m0 and m00 : In this case condition (30) holds and takes
the form
h
xa 1 ux m0
h
xa 1 ux m00
= xa
t
tC
uw m00
+ ^ t+1 kt+1 wx m0
ux m0
i
tC
ux m00
+ ^ t+1 kt+1 wx m00
w
t C
uw m00
uw m0
w
t C
i
uw m0
:
Since ux ; uw lie in a compact set, taking sequence xn ! 0 we get, invoking upper-hemicontinuity
again,
h
tC
0
u
0
m
+^
t+1 kt+1
which violates Lemma 15.
8.5
w
0
0
m
i
h
tC
0
u
00
m
+^
t+1 kt+1
w
0
m
00
i
= 0;
Arguments for case with persistent types
In the following proofs we assume that the set of feasible utility is bounded and, without loss
of generality, we set the lower bound to 0. Also, we assume that the message set Mt chosen by
the planner is …nite for all t. The proof that in the worst equilibrium there is no information
xvi
revelation to the government is the same as in the iid case. The payo¤ of this equilibrium
depends on the government’s information that dissipates slowly due to the persistence of the
shocks. Thus, the best payo¤ for a government that deviates at time t is
~ t ( t) =
W
sup
fut+s (h)gh2H t ;s
0
Z
1
X
s
H t s=0
Ept+s [ jh] ut+s (h) d
t
(66)
subject to the feasibility constraint (8) holding for all t + s and
Z
s
j
pt d jht for s > 0:
pt+s jht =
This payo¤ is a generalization of (7) in the iid case. Similarly to that case, we can bound
~
Wt ( t ) with a function that is linear in t 1 : Given p 2 ( ), de…ne the analogue of (13) as
R s
!
Z
1
(d s j ) s ut+s (m)
X
s
:
Wt ( ; p) =
sup
(dmj ) d j
p d
w
fut+s (m)gs 0
(C
(u
(m))
e)
t+s
s=0
t;t+s
Mt
(67)
As in the iid case, let uw
t+s (m) denote the solution to (67), which is given by equation
Ept+s [ jm] =
w
t;t+s C
uw
t+s (m) .
By Langrange duality we can prove the analogue of Lemma 2 in the iid case.
Lemma 17 The multiplier
w
t;t+s
is uniformly bounded away from 0 and belongs to a com-
pact set for all t and s. Therefore, uw
t+s (m) belongs to a compact set in the interior of
[(1
) v; (1
) v] for all m; ; t; s:
Function Wt is well de…ned, continuous, convex in
t,
if and only if
t 1
is uninformative. For any
Z
~ t ( t)
Wt
W
Ht
with equality if
t ; pt ;
t 1
=
t ; pt ;
jht ;
t
Z
^t ;
t;p
t 1
uniformly bounded in t, and is minimized
,
; pt ht
1
d
t 1 dz;
(68)
:
Proof. The objective function (66) is concave and the constraint set is convex and we can
~ t ( t ) as
use the Lagrange duality and rewrite W
R
(
)
P1 s
Ept+s [ jh] ut+s (h) d t dz
t Z
s=0
H
~ t ( t) =
R
P1 s
W
min
sup
:
e
f t;s 0gs 0 fut+s (h)g
t;t+s
s=0
t
H t Z C (ut+s (h)) d t dz
h2H ;s 0
(69)
Let
w
t;t+s
be the solution to the minimization problem. Since after deviating, the government
~ t period by period.
doesn’t provide incentives, we can maximize W
Z
s
w
w
sup
Ept+s [ jh] ut+s (h)
t;t+s C (ut+s (h)) + t;t+s e d t dz:
fut+s (h)gh2H t ;s
0
Ht Z
xvii
w
t;t+s
By using the same argument as in the iid case we can show that
is uniformly bounded
away from 0 and uniformly bounded above for all s. This also proves that supremum in (69)
is achieved. Also,
~ t ( t) =
W
f
min
t;s
0gs
max
fut+s (h)gh2H t ;s
0
max
fut+s (h)gh2H t ;s
0
Z
0
R
(
1
X
s
H t Z s=0
P1
s=0
Ht Z
P1 s
t;t+s
s=0
: Since
t 1
max
fut+s (h)gh2H t ;s
=
Z
Ht 1
0
Z
Ht
max
Z fut+s (m)gs
0
Mt
1
X
s
Z s=0
Z
w
t;t+s g
Ht Z
)
d j
C (ut+s (h)) d t dz
w
t;t+s (C
(ut+s (h))
e
)
e) d t dz
may not be a minimizer for an arbitrary
w
t;t+s (C
Ept+s [ jh] ut+s (h)
t (dmj
R
Ept+s [ jh] ut+s (h) d t dz
Ept+s [ jh] ut+s (h)
where the inequality follows from the fact that f
t ; pt ;
s
1
X
pt d
s=0
equation (68) must hold.
(ut+s (h))
2
s4
R
e) d t dz
s (d
sj
)
3
ut+s (m) 5
d
w
(C
(u
(m))
e)
t+s
t;t+s
s
t 1 dz
The same arguments show that we can maximize (67) period by period, thus, if we let
R s
!
Z
(d s j ) s ut+s (m)
^ t+s ( t ; pt ) = max
W
d j
pt d
;
t (dmj )
w
fut+s (m)g
e)
t;t+s (C (ut+s (m))
Mt
the optimal uw
t+s (m) satis…es
1
C 0 (ut+s (m)) =
w
t;t+s
Z
p d
E
jm;
2
^ t+s is uniformly bounded in t + s,
which implies that W
1
;
w
t;t+s
j j
w
t;t+s
;
t,
and pt and that we can re^ t+s by the Theorem
strict ut+s (m) to a compact set. The latter implies continuity of W
^ t+s is uniformly bounded, we have that Wt ( t ; pt ) =
of the Maximum. Finally, since W
P1 s ^
Wt+s ( t ; pt ) is also bounded and continuous.
s=0
The proof that Wt is convex in
t
follows exactly the same steps as the in the iid case.
To see that Wt is minimized at an uninformative signal, let
be uninformative and note
that for any
Wt ( t ; pt ) =
max
fut+s (m)gs
max
fut+s gs
0
0
Z
Mt
Z
t (dmj
d j
pt d
)
d j
1
X
s=0
= Wt ( t ; pt )
xviii
pt d
1
X
s=0
s
s ut+s
2
s4
w
t;t+s (C
R
3
u
(m)
s
t+s
5
w
e)
t;t+s (C (ut+s (m))
s (d
(ut+s )
sj )
e)
Let
(A) =
R
(Aj ) (d ) for any Borel A of message set Mt and let uw
t+s be the optimal
solution when the strategy is uninformative, then
Wt ( t ; pt )
=
max
fut+s (m)gs
0
Wt ( t ; pt )
Z
t (dmj )
Mt
20
Z
1
X
s 4@
s
s=0
(d s j )
d j
pt d
1
s A ut+s (m)
w
t;t+s (C
(ut+s (m))
The expression in square bracket is non-negative. Moreover, if
is a set of messages A with
(A) > 0 such that jE [ jA]
uw
t+s
e)
t
w
t;t+s
C uw
t+s
is informative, then there
3
e 5
1j > 0: For all such messages
the expression in square brackets is strictly positive since uw
t does not satisfy the optimality
condition
1
C 0 (ut (m)) =
for m 2 A: Since
mative
(A) > 0; Wt ( t ; pt )
w E
t;t
[ jA]
Wt ( t ; pt ) is strictly positive and, hence, any infor-
cannot be a minimum.
Similarly to the iid case, we replace the incentive constraint for the government E
~ t ( t ) with
W
E
1
X
t s
Z
t ut
Wt
Ht
t=s
t
Z
jht ;
; pt ht
1
d
t 1 dz
P1
t s
t=s
(70)
and use standard techniques to derive the analogue of the Langrangian (17) for the persistent
case. The problem becomes
1
X
L = max E
u;
subject to
pt
for all ht
1 ; ht
t
jh
=R
R
t [ t ut
tC
(ut )
t Wt ]
(71)
t=0
mjht ;
t
t
j
mjht ;
pt
d j
1
pt
jht
d
1
d
and m; whenever de…ned, the incentive constraint
#
" 1
#
" 1
X
X
t
t
for all
E 0
u
E
u
t=0
1
;
jht
0
;
1
;
(72)
t=0
and
E
"
1
X
t
#
u v = v;
t=0
xix
(73)
t ut
1
for some non-negative sequences of Lagrange multipliers
t ; t ; t t=0 with the property that
^
with strict inequality if and only if (70) binds in period t.
t
t= t 1
Finally, we adapt the arguments in Fernandes and Phelan (2000) with minor modi…cations
and obtain a recursive representation of (71). In particular, we …rst rewrite the constranit
set in a recursive form by adding the promise-keeping constraint (34) for each type
. Since
it is no longer optimal for agents to always report their types truthfully, unlike in the case
studied in Fernandes and Phelan (2000), the agent’s previous type,
, cannot be used as a
state variable. Instead, the recursive formulation keeps track of the planner’s posterion beliefs
about
. Therefore,
kt (v; p) =
max
fu;w; g
( j )2 (M );p0 2 ( )
Z
p d
E
h
i
0
^
t C (u) + t+1 kt+1 w; p j
u
t
Z
Wt dz
(74)
subject to (34),
R
0
p ( jm; z) = R
(mj ; z)
(mj ; z)
j
p d
d j
p d
whenever de…ned, the incentive constraint
E [ u + w ( ; ; ) j ; z]
E 0 [ u + w ( ; ; ) j ; z] for all z; ;
0
:
(75)
We now extend the arguments of the simple example in Section 4.1 to the persistent case.
As in the iid case, the assumption that the government can deviate at time t
1 only if it
deviates at t = 0 implies that the Lagrangian (71) can be written as
( 1
)
X
t
L = max E
t C (ut )
0 W0
u;
t=0
subject to (72) and (73). Consider the subgame starting from t = 1. From past reports, the
planner has beliefs p 2
not bind at t
( ). Also, as in the iid case, since the sustainability constraint does
1, the standard Revelation principle applies and the agent will report his type
truthfully (let m denote the message corresponding to type .) Thus, as in Fernandes and
Phelan (2000), from time t
type. At time 1, let
1 (v; p)
2 we can replace the posterior of the planner with the agent’s
1 (v; p)
=
be de…ned as
max
fu(m);w(m; )gm2M
1; 2
subject to
v
i
=
X
m;
j
i
X
p
i
E
1C
(u) +
2 (w;
i
u (m ) + w (m ; ) j
xx
i
; 8i
)j
i
and
u m0 + w m0 ;
u (m ) + w (m ; )
The constraints are linear in (u; w), hence, if (u; w),
2 (w;
; 8m ; m0 ; :
), and
equation for some (v; p), it is immediate to see that (x u; x w),
also solve the Bellman equation for (x v; p) ; x > 0. Thus,
1 (v; p)
xa
1 (v; p)
solve the Bellman
2 (w;
), and xa
1 (v; p)
is homogenous in v. Also,
since the objective function is linear in p and the constraints are independent of p,
1 (v; p)
is
convex in p.
At time 0, for any reporting strategy
0 (v;
)=
2
(M0 ) ; let
max
E [
fu(m);w(m; )gm2M
0 (v;
0C
) be de…ned as
(u) +
1 (w; p)]
0; 2
subject to
p ( jm) = P
(mj )
( ;
whenever de…ned, (34), and (75), where
linear in (u; w) and
If
=
un
)2
P
2
2
(mj )
j
j
is the planner’s initial prior. Again, constraints are
1 (v; p)
is homogenous in v, thus, 0 (v; ) will also be homogenous in v.
P
P
un (mj )
j
> 0, then
is uninformative and Pr (m) =
2
2
p ( jm) =
un
(mj )
P
2
j
=
Pr (m)
X
2
j
:
and the optimal allocation (uun ; wun ) is uun (m) = u and wun (m; ) = w ( ) for all . Suppose
instead that
is informative, then there exist m0 , m00 , and
By convexity of
1
in p,
E
1
wun ; pin
E [
1 (w
un
such that pin ( jm0 ) 6= pin ( jm00 ).
; pun )] :
Finally, if the distribution of types is such that no bunching is desirable under commitment,
the latter implies
0 (v;
)>
0 (v;
un ).
To prove Proposition 5 we need the following Lemma.
Lemma 18 Pr (uv;p (m; z) ! 0) ! 1 and Pr (wv;p (m; z; ) ! 0) ! 1 as v ! 0, for all m; ;
and p.
xxi
Proof. From (34) for all p we have
Z
d j
v
=
v;p (dmj )
Z Mt Z
d j
[ uv;p (m; z) +
=
Z
Z
d j
[ uv;p (m;
~ z) +
Z
Z
[ uv;p (m;
~ z) + wv;p (m;
~ z;
ZZ
wv;p (m; z; ) dz, 8m; :
[ uv;p (m; z) + wv;p (m; z; )] dz
wv;p (m; z; )] dz, m 2 Supp (
v;p (
j ))
wv;p (m;
~ z; )] dz, 8m
~
)] dz, 8m;
~ .
Z
Here the fourth and …fth lines follow from nonnegativity of u and w; and the third line follows
R
from (75). Thus, limv!0 Z wv;p (m; z; ) dz = 0, 8m; ; p: Analogous arguments prove that
R
limv!0 Z uv;p (m; z) dz = 0, 8m; p. Since uv;p and wv;p are bounded below by 0; the latter
implies that Pr (uv;p (m; z) ! 0) ! 1 and Pr (wv;p (m; z; ) ! 0) ! 1 for all m; ; and p.
Proof of Proposition 5. Let
Z
uv;p (m; z) =
Mt
be any uninformative strategy. Let
d j
d
v;p (dmj
) uv;p (m; z)
and
wv;p (m; z; ) =
1
Z
v;p (dmj
) [ uv;p (m; z) + wv;p (m; z; )]
1
uv;p (m; z) :
Mt
Pro…le (uv;p ; wv;;p ; ) is incentive compatible and satis…es
Z
d j
[ uv;p (m; z) + wv;p (m; z; )] dz
v;p (dmj )
Mt Z
Z
[ uv;p (m; z) + wv;p (m; z; )] dz
=
d j
Z
Z
Z
=
d j
uv;p (m; z) +
v;p (dmj ) [ uv;p (m; z) + wv;p (m; z; )]
Z
Mt
Z
=
d j
[ uv;p (m; z) + wv;p (m; z; )] dz = v
v;p (dmj )
uv;p (m; z) dz
Mt Z
Therefore the value of the objective function (74) evaluated at (uv;p ; wv;p ;
v;p )
should be
higher than evaluated at (uv;p ; wv;p ; ) ;
Z
Z
p d
E
p d
E
Z
Z
uv;p
v;p
v;p
h
uv;p
tC
(uv;p ) + ^ t+1 kt+1 (wv;p ; p0 )
t Wt ( v;p ; p)
0
^
t C (uv;p ) + t+1 kt+1 wv;p ; p
xxii
dz
t Wt ( ; p) j
(76)
i
dz
From Lemma 18, Pr (uv;p (m; z) ! 0) ! 1 and Pr (wv;p (m; z; ) ! 0) ! 1 for all m; ; and p
and, thus, Pr (uv;p (m; z) ! 0) ! 1 and Pr (wv;p (m; z; ) ! 0) ! 1 for all m; ; and p: Also,
similarly to the iid case, Lemma 3 in Acemoglu et al. (2008) implies that it is su¢ cient to
randomize among only a …nite number of points fuv;p ; wv;p ;
Z
v;p (dmj
)
d j
Mt Z
t
Z
(Wt (
v;p ; p)
R
t Z
for all p. Since Wt (
Pr (
v;p
(uv;p (m) uv;p (m))
C (uv;p (m)))
t (C (uv;p (m))
0
^
+ t+1 (kt+1 (wv;p ; p ) kt+1 (wv;p ; p0 ))
Wt ( ; p)) dz
(Wt (
v;p ; p)
Wt ( ; p)) dz. Hence, in the limit equation (76) becomes
Z
lim sup t
(Wt ( ; p) Wt ( v;p ; p)) dz 0;
v!0
uous in
Therefore, for each p
Z
converges to
Pr (Wt (
p d
v;p g.
v;p ; p)
v;p ; p)
Z
Wt ( ; p) by Lemma 17 and
t
> 0 by assumption,
! Wt ( ; p)) ! 1 as v ! 0 for all p: By Lemma 17, Wt ( ; p) is contin-
and achieves its minimum only at uninformative reporting strategies, therefore
! ) ! 1 for all p:
xxiii
dz
© Copyright 2026